1.3 Access Manager Devices and Their Features
1.3.1 Administration Console
The Administration Console is the central configuration and management tool for the product. It is a modified version of iManager that can be used only to manage the Access Manager components. It contains a Dashboard option, which allows you to assess the health of all Access Manager components.
Figure 1-3 NetIQ Access Manager Dashboard Page
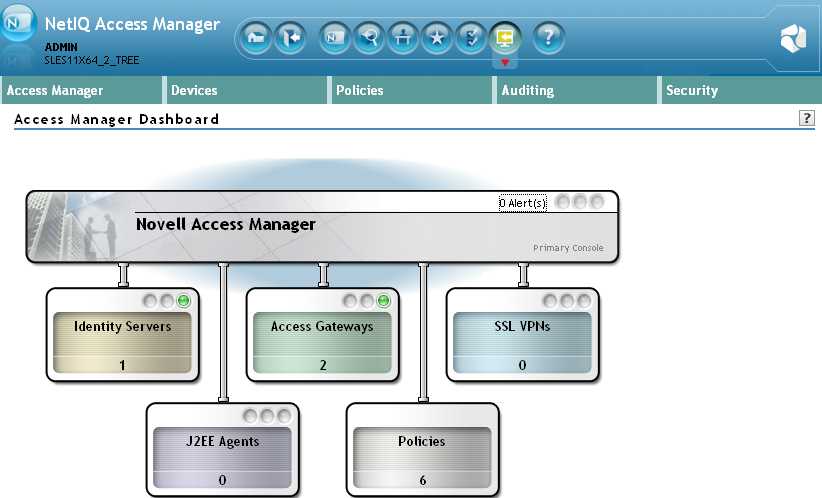
The Administration Console also allows you to configure and manage each component, and allows you to centrally manage resources, such as policies, hardware, and certificates, which are used by multiple components.
1.3.2 Identity Servers
The Identity Server is the central authentication and identity access point for all other services. It is responsible for authenticating users and distributing role information to facilitate authorization decisions. It also provides the Liberty Alliance Web Service Framework to distribute identity information.
An Identity Server always operates as an identity provider and can optionally be configured to run as an identity consumer (also known as a service provider), using Liberty, SAML 1.1, or SAML 2.0 protocols. As an identity provider, the Identity Server validates authentications against the supported identity user store, and is the heart of the user’s identity federations or account linkage information.
In an Access Manager configuration, the Identity Server is responsible for managing:
-
Authentication: Verifies user identities through various forms of authentication, both local (user supplied) and indirect (supplied by external providers). The identity information can be some characteristic attribute of the user, such as a role, e-mail address, name, or job description.
-
Identity Stores: Links to user identities stored in eDirectory, Microsoft Active Directory, or Sun ONE Directory Server.
-
Identity Federation: Enables user identity federation and provides access to Liberty-enabled services.
-
Account Provisioning: Enables service provider account provisioning, which automatically creates user accounts during a federation request.
-
Custom Attribute Mapping: Allows you to define custom attributes by mapping Liberty Alliance keywords to LDAP-accessible data, in addition to the available Liberty Alliance Employee and Person profiles.
-
SAML Assertions: Processes and generates SAML assertions. Using SAML assertions in each Access Manager component protects confidential information by removing the need to pass user credentials between the components to handle session management.
-
Single Sign-on and Logout: Enables users to log in only once to gain access to multiple applications and platforms. Single sign-on and single logout are primary features of Access Manager and are achieved after the federation and trust model is configured among trusted providers and the components of Access Manager.
-
Identity Integration: Provides authentication and identity services to Access Gateways that are configured to protect Web servers, Java* applications, and SSL VPN. The Access Gateway and other Access Manager components include an embedded service provider that is trusted by NetIQ Access Manager Identity Servers.
-
Roles: Provides RBAC (role-based access control) management. RBAC is used to provide a convenient way to assign a user to a particular job function or set of permissions within an enterprise, in order to control access. The identity provider service establishes the active set of roles for a user session each time the user is authenticated. Roles can be assigned to particular subsets of users based on constraints outlined in a role policy. The established roles can then be used in authorization policies and J2EE permissions, to form the basis for granting and restricting access to particular Web resources.
-
Clustering: Adds capacity and failover management. An Identity Server can be a member of a cluster of Identity Servers, and the cluster is configured to act as a single server.
For an overview of Liberty, see About Liberty
in the NetIQ Access Manager 3.2 SP3 Identity Server Guide.
For an overview of SAML, see Understanding How Access Manager Uses SAML
in the NetIQ Access Manager 3.2 SP3 Identity Server Guide.
1.3.3 Access Gateways
An Access Gateway provides secure access to existing HTTP-based Web servers. It provides the typical security services (authorization, single sign-on, and data encryption) previously provided by Novell iChain, and is integrated with the new identity and policy services of Access Manager.
Figure 1-4 Access Gateway Component

The Access Gateway is designed to work with the Identity Server to enable single sign-on to protected Web services. The following features facilitate single sign-on to Web servers that are configured to enforce authentication or authorization policies:
-
Identity Injection: Injects the information the Web server requires into HTTP headers.
-
Form Fill: Automatically fills in requested form information.
If your Web servers have not been configured to enforce authentication and authorization, you can configure the Access Gateway to provide these services. Authentication contracts and authorization policies can be assigned so that they protect the entire Web server, a single page, or somewhere in between.
The Access Gateway can also be configured so that it caches requested pages. When the user meets the authentication and authorization requirements, the user is sent the page from cache rather than requesting it from the Web server, which can increase content delivery performance.
Access Manager 3.2 onwards, there are two types of Access Gateways. Both are based on the same core technology and differ only in their deployment method.
Access Gateway Appliance: It is installed as a soft appliance, which includes the operating system.
Access Gateway Service: It requires you to provide the operating system.
Previous versions of Access Manager also provided a flexible deployment model for the Access Gateway that included both an appliance option (Linux Access Gateway) and a service option (Access Gateway Service). Features of the Access Gateway Appliance and the Access Gateway Service are same but differ from the Linux Access Gateway.
For more information about the differences, see Section D.0, Feature Comparison of Different Types of Access Gateways.
For information about how to upgrade or migration your chosen Access Gateway technology, see Upgrading Access Manager
in the NetIQ Access Manager 3.2 SP3 Migration and Upgrade Guide.
1.3.4 SSL VPN
The SSL VPN server provides secure access to non-HTTP based applications, such as e-mail servers, FTP services, or Telnet services. The SSL VPN server is a Linux-based service that can be installed in two modes:
-
As a resource accelerated by and protected by the Access Gateway, which shares session information with the SSL VPN server
-
As a stand-alone device with an Embedded Service Provider, which allows the SSL VPN server to establish its own relationship with the Identity Server.
An ActiveX plug-in or Java applet is delivered to the client on successful authentication. Roles and policies determine authorization decisions for back-end applications. Client integrity checking is available to ensure the existence of approved firewall and virus scanning software, before the SSL VPN session is established.
1.3.5 J2EE Agents
You install and configure the J2EE Agent components only when you need fine-grained access control to Java applications. Access Manager provides JBoss, WebLogic, and IBM WebSphere server agents for Java 2 Enterprise Edition (J2EE) application servers.
These agents leverage the Java Authentication and Authorization Service (JAAS) and Java Authorization Contract for Containers (JACC) standards for Access Manager-controlled authentication and authorization to Java Web applications and Enterprise JavaBeans*. For more information about these Java authentication and authorization standards, see the JAAS Authentication Tutorial and Java Authorization Contract for Containers.
Like the Access Gateway, J2EE Agents are federation-enabled and therefore operate as service provider agents. As such, they redirect all authentication requests to the Identity Server, which returns a SAML assertion to the component. This process has the added security benefit of removing the need to pass user credentials between the components to handle session management.
1.3.6 Policies
Policies provide the authorization component of Access Manager. The administrator of the Identity Server can use policies to define how properties of a user’s authenticated identity map to the set of active roles for the user. This role definition serves as the starting point for role-based authorization policies of the Access Gateway and J2EE components. Additionally, authorization policies can be defined that control access to protected resources based on user and system attributes other than assigned roles.
The flexibility built into the policy component is nearly unlimited. You can, for example, set up a policy that permits or denies access to a protected Web site, depending on user roles (such as employee or manager), the value of an LDAP attribute, or the user’s IP address.
Each Access Gateway and J2EE component includes an Embedded Service Provider agent that interacts with the Identity Server to provide authentication, policy decision, and enforcement. For the Java application servers, the agent also provides role pass-through to allow integration with the Java Application server’s authorization processes. For Web application servers, the Access Gateway provides the ability to inject the user’s roles into HTTP headers to allow integration with the Web server’s authorization processes.
1.3.7 Certificate Management
Access Manager includes a certificate management service, which allows you to manage the certificates used for digital signatures and data encryption. You can create locally signed certificates or import externally signed certificates, then assign these certificates to the trust stores and keystores of the following components:
-
Identity Server: Certificates allow you to provide secure authentication to the Identity Server and enable encrypted content from the Identity Server portal, via HTTPS. They also provide secure communications between trusted Identity Servers and user stores.
-
Access Gateway: Uses server certificates and trusted roots to protect Web servers, provide single sign-on, and enable the product's data confidentiality features, such as encryption.
-
SSL VPN: Uses server certificates and trusted roots to secure access to non-HTTP applications.
-
J2EE Agents: The embedded service providers that NetIQ provides for the J2EE Agents use signing and SSL certificates. Access Manager’s certificate management features can manage certificates for your J2EE application servers if the application server uses one of the supported keystore types: Java Key Store (JKS) eDirectory, PKCS12 (.pfx), or DER (.cer).
You can install and distribute certificates to the Access Manager components and configure how the components use certificates. This includes central storage, distribution, and expired certificate renewal.
1.3.8 Auditing and Logging
Access Manager supports audit logging and file logging at the component level. A licensed version of Novell Audit is included to provide compliance assurance logging and to maintain audit log entries that can be subsequently included in reports. Each component creates assurance log entries to show the effect of each policy statement on each access control decision. Log entries include events such as notifications pertaining to the operational state of Access Manager components, the results of administrator and user requests, and policy actions invoked in determining request results.
The Access Manager devices can be configured to send their auditing events to a Sentinel™ or a Sentinel Log Manager server.
The following procedure helps you configure Access Manager for Windows Auditing:
-
Get the batch script for Windows from Windows Auditing Configuration Script and run the script on the Administration Console.
-
Enter the credential details.
-
Once the script is complete, close the command prompt.
NOTE:You can manually delete the temporary files that are created after installation.
1.3.9 Embedded Service Provider
The Access Gateway, SSL VPN server, and J2EE Agent use an Embedded Service Provider to redirect authentication requests to the Identity Server. The Identity Server requires requests to be digitally signed and encrypted and allows only trusted devices to participate. To become trusted, devices must exchange metadata. The Embedded Service Provider performs this task automatically for the Access Gateway, SSL VPN server, and J2EE Agent.
1.3.10 The User Portal Application
The Access Manager User Portal is a customizable application where end users can access and manage their authentications, federations, and profile data. The authentication methods you create in the Administration Console are reflected in the Portal.
Figure 1-5 Access Manager User Portal
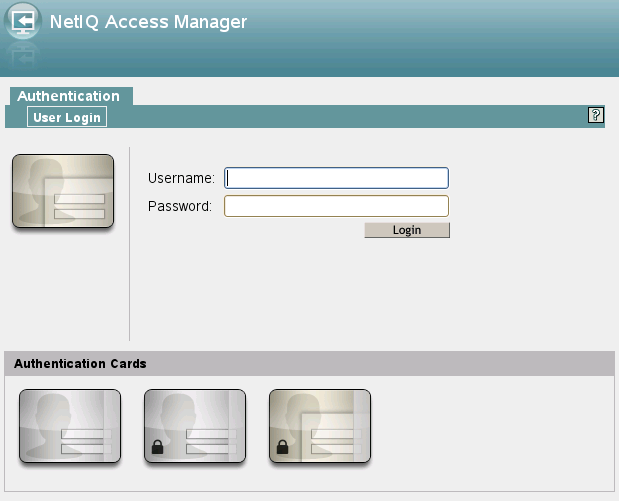
Help information for the end users is provided in the user interface. If you know how to customize JSP* pages, you can customize the portal for rebranding purposes and for creating custom login pages.
1.3.11 Language Support
The Access Manager software for installation and administration uses English and is not localized. The Administration Console is also not localized and uses only English. However, the client pieces of Access Manager are either localized or allow you to create custom pages.
-
The User Portal, which appears when the user logs directly into the Identity Server, is localized and so is its help file.
-
The SSL VPN client, which displays when the user establishes an SSL VPN session, is also localized.
The User Portal and the SSL VPN client are localized for German, French, Spanish, Italian, Japanese, Portuguese, Dutch, Chinese (Simplified), and Chinese (Traditional). The language must be set in the client’s browser to display a language other than English.
The Access Gateway and Identity Server, which can send messages to users when an error occurs, allow you to customize the error pages, but you are responsible for supplying the content of the customized pages. For information on customizing these pages, see the following:
-
For the Access Gateway Appliance and Service, see
Customizing Error Messages and Error Pages on Access Gateway
in the NetIQ Access Manager 3.2 SP3 Access Gateway Guide. -
For the Identity Server, see
Customizing Identity Server Messages
in the NetIQ Access Manager 3.2 SP3 Identity Server Guide.