12.10 User Configurations
You must have the user permission in order to work in the User Configuration window.
User configuration allows you to:
NOTE:The Sentinel Database Administrator, Sentinel Administrator, Sentinel Application User, and Sentinel Report User are created during installation.
12.10.1 Opening the User Manager Window
-
Click the tab.
-
Click .
12.10.2 Creating a User Account
In order to meet stringent security configurations required by Common Criteria Certification, Sentinel requires a strong password with the following characteristics:
-
Select passwords of at least 8 with characters in length that includes at least one uppercase letter, one lower case letter, one special symbol (!@#$%^&*()_+), and one numeral (0-9).
-
Your password should not contain your e-mail name or any part of your full name.
-
Your password should not be a common word. For example, it should not be a word in the dictionary or slang in common use.
-
Your password should not contain words from any language, because numerous password-cracking programs exist that can run through millions of possible word combinations in seconds.
-
You should select a password you can remember that is still complex. For example, Msi5!YOld (My Son is 5 years old) or IhliCf5#yN (I have lived in California for 5 years now).
NOTE:Do not use \ and ‘ in the username and password because the database does not allow these characters.
To use this feature, you must have the User Management user permission. For more information, see the Sentinel 6.1 Rapid Deployment Reference Guide.
Creating a Local User Account for Sentinel
-
Select the tab.
-
Open the folder.
-
Open the window.
-
Click
or
Right-click any user and select .

-
Under Authorization:
-
Select Local for Authentication.
-
Specify the username.
-
Specify the password.
-
Confirm the password.
-
-
For a Security Filter, click the down-arrow. The Filter Selection window displays and shows all public filters.
-
Select a filter and click or click to create, then select a new filter.
After assigning a security filter to a user, you cannot delete that filter.
-
(Optional) Under , specify:
-
First Name
-
Last Name
-
Department
-
Phone
-
Email
-
-
Click the tab and assign user permissions.
-
Click the tab and select an iTRAC workflow role for the user.
-
Click .
Creating an LDAP User Account for Sentinel
NOTE:This option is applicable only for Sentinel Rapid Deployment SP1 and later. By default, this option is disabled. Configure the server as given in LDAP Authentication
in the Sentinel Rapid Deployment Install Guide to enable this option.
-
Select the tab.
-
Expand the folder in the navigation tree.
-
Select .
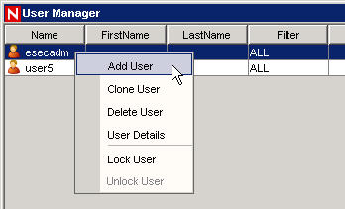
The User Manager window is displayed.
-
Click or right-click any user and select .
The Add User window is displayed.
-
In the Add user window, perform the following:
-
Select for authentication.
-
Specify the LDAP username based on the value you specified for
Anonymous searches on LDAP directory:
parameter while configuring LDAP authentication.-
y: The must be the same as the eDirectory username or Active Directory sAMAccountName.
-
n: The need not be the same as the eDirectory username or Active Directory sAMAccountName.
-
-
Click the drop-down arrow on the drop-down list.
The Filter Selection window is displayed that lists all the public filters.
-
Select a filter, and click or click to create a filter, then select the new filter.
After assigning a security filter to a user, you cannot delete that filter.
-
-
Specify the fully qualified Distinguished Name of the LDAP user in the field. Do not leave the field empty.
For example:
eDirectory User: cn=sentinel_ldap_user,o=novell
Active Directory User: cn=sentinel_ldap_user,cn=users,dc=test,dc=com
This field is available only if you have specified n for
Anonymous searches on LDAP directory:
parameter while configuring LDAP authentication. For more information, seeLDAP Authentication
in the Sentinel Rapid Deployment Installation Guide.NOTE:If you had opted to perform anonymous searches when you had last run the ldap_auth_config script, and now you do not want to perform anonymous searches:
Run the script ldap_auth_config script again, and specify n for
Anonymous searches on LDAP directory:
. For each existing LDAP user, right-click and select and specify the fully qualified DN of the LDAP user in the field.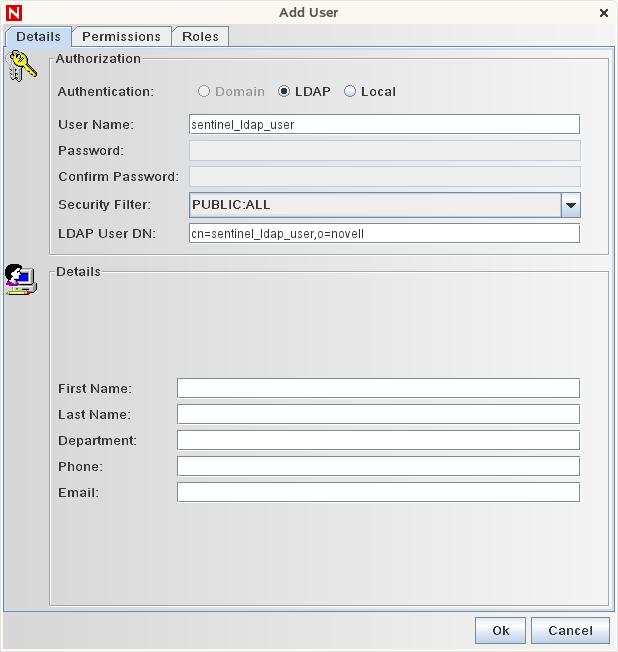
-
(Optional) Under , specify the following:
-
-
Click the tab and assign user permissions. For more information about permissions, see
Sentinel 6.1 Rapid Deployment Control Center User Permissions
in the Sentinel Rapid Deployment Reference Guide.. -
Click the tab and select an iTRAC workflow role for the user. This affects what work items appear in the user’s work list.
-
Click .
-
You can now log in to Sentinel Rapid Deployment Web user interface, Sentinel Control Center, and Sentinel Solution Designer by using your LDAP username and password.
Creating a Domain User Account for Sentinel
NOTE:This option is applicable only in Sentinel Rapid Deployment Hotfix 2 and is used to create LDAP user accounts.
-
Select the tab.
-
Open the folder.
-
Open the User Manager window.
Click a new User.
or
Right-click any user and select .
-
Under Authorization:
-
Select Domain authentication.
-
Specify an existing User Name in the form Domain\Username.
-
-
For Security Filter, click the down-arrow. The Filter Selection window displays and shows all public filters.
-
Select a filter and click or click to create and then select a new filter.
After assigning a security filter to a user, you cannot delete that filter.
(Optional) Under Details, specify:
-
First Name
-
Last Name
-
Department
-
Phone
-
Email
-
-
Click the Permissions tab and assign user permissions. For more information about permissions, see
Sentinel 6.1 Rapid Deployment Control Center User Permissions
in the Sentinel 6.1 Rapid Deployment Reference Guide. -
Click the Roles tab and select an iTRAC workflow role for the user. This affects what work items appear in the user’s work list.
-
Click .
NOTE:PostgreSQL does not allow the creation of users named the same as one of the PostgreSQL Reserved words. Also, Sentinel does not allow you to use these names.
12.10.3 Modifying a User Account
To use this feature, you must have the User Management permission.
NOTE:The Sentinel Database Administrator, Sentinel Administrator, Sentinel Application User, and Sentinel Report User are created during installation.
-
Open the User Manager window.
-
Double-click a user account or right-click it, then click .
-
Modify the account.
-
Click .
12.10.4 Viewing Details of a User Account
To use this feature, you must have the User Management permission.
-
Open the User Manager window.
-
Double-click a user account or right-click it, then click .
Review the details of the user account and close the window.
12.10.5 Cloning a User Account
-
Open the User Manager window.
-
Right-click a user account, then click .
-
Change the user information and the user permissions.
-
Click .
12.10.6 Deleting a User Account
To use this feature, you must have the User Management permission.
-
Open the User Manager window.
-
Right-click a user account, then click .
-
A Delete box displays. Click to delete the User.
12.10.7 Terminating an Active User Session
-
Open the Active User Sessions window.
-
Right-click an active session you want to terminate, then click .
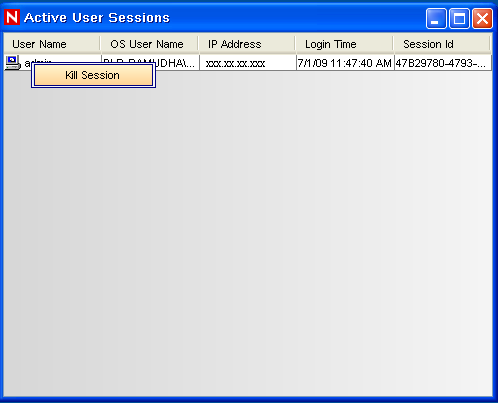
You are prompted for a termination message. This option is provided so that you can inform the user why you are killing the session.
-
Provide a message, then click .
or
Close the window to terminate the session without sending a message.
NOTE:If the client machine has multiple network interfaces, the IP Address displayed in the Active User Sessions window might not be the desired IP address, as the non-loop back IP address of the first NetworkInterface returned by the system is displayed.
12.10.8 Adding an iTRAC Role
-
Open the Role Manager window.
-
Right-click a role, then click .
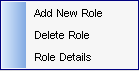
12.10.9 Deleting an iTRAC Role
-
Open the Role Manager window.
-
Right-click a role, then click .
12.10.10 Viewing the Details of a Role
-
Open the Role Manager window.
-
Right-click a role, then click .