4.1 Security Mechanisms for Access Control
Operations Center provides three mechanisms for access control:
4.1.1 Operations Center Administrator Account
The Operations Center Administrator user account has supreme administrative authority within the Operations Center environment. Operations Center installs with a default Administrator account and password. You can change the password for the Operations Center administrator through the Operations Server console. In fact, it is strongly recommended that the administrator change the password immediately after logging into the system for the first time.
If the external identification and authentication option is deployed, the Operations Center Administrator account remains independent of the external LDAP authentication methods. This enables the Operations Center administrator to log in to Operations Center even if the Operations Center server is configured to use an I&A module other than its native I&A method. This ensures that the Operations Center administrator can perform critical Operations Center administrative functions even if the external I&A mechanism is changed or becomes dysfunctional.
If the Business Service Dashboard component is deployed, the Operations Center Administrator account has supreme authority in the dashboard environment as well.
The Operations Center software Administrator account uses a standard default password. To prevent unauthorized access to Operations Center software by other users, you should change the administrator’s password to a new password known only to you.
To change the Administrator password:
-
Click File > Change Password.
-
In the Change Password dialog box, enter the new password in the New password and New password (again) fields.
-
Click OK.
The password is updated.
4.1.2 Operations Center Security Manager
User names, passwords, and security permissions must be specified to allow access to the Operations Center environment.
The Operations Center Security Manager manages all authorization data and enforces access control. Access control is defined by using access control lists (ACLs) similar to those that exist in common operating systems. You can grant or deny users and groups of users permissions to elements managed by Operations Center. Defining access privileges for elements is explained in Section 4.5, Assigning Access Privileges.
A summary of the Operations Center permissions is listed below. The privileges are not cumulative. For example, both View and Manage permissions must be assigned to a user to enable the user to view elements and their properties, and also to change the property values or add new custom properties.
Permissions can be granted or denied. Deny permissions take precedence.
-
View: The user can view elements and related components such as property sheets and alarms.
-
Access: The user can connect to remote elements managed in the Operations Center environment, including elements on remote servers.
-
Manage: The user can perform update actions such as editing property pages, creating custom properties on an element, acknowledging or clearing alarms, and performing nonintrusive actions such as Ping or TraceRoute.
-
Define: The user can perform administrative tasks such as adding, removing or changing scripts, sites, and administrative elements such as calendars, jobs, automations, and operations, as well as creating and changing the definition of adapters, service model elements and SLAs.
Operations Center is constructed much like an X.500 directory in that it allows you to set permissions at any level of the element hierarchy and have those permissions automatically inherited by child elements in the hierarchy. You can revoke permissions at any level of the hierarchy and prevent inheritance from continuing through the hierarchy. When an element is assigned explicit permissions, it no longer automatically inherits from its parents.
Operations Center Dashboard
The Operations Center Dashboard leverages user and group accounts from the Operations Center server to give users access to the dashboard portal pages and Operations Center data via the dashboard portlets. In the dashboard’s control panel, you can grant or deny users and groups of users permissions over portal pages and content. For more information about dashboard and portal security, see Section 7.0, Dashboard Security.
4.1.3 Delegated Administration
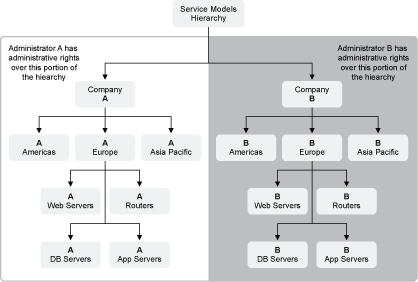
The Operations Center access control model allows delegated administration of any portion of the element hierarchies. For example, in an MSP environment, use permissions to delegate administrative rights over portions of the Service Models element hierarchy so that customers can administer their own portions of the environment. Perhaps the customer wants to retain the ability to define new business views, manage existing business views, manage users and groups within their views, and so on.
Consider an example where an MSP supports two serviced customers, A and B, within a single Operations Center environment. Both customers are provided the same service. The MSP can create two separate branches within the Operations Center Service Models element hierarchy to represent each customer, then delegate the administrative rights to each branch to an individual administrator.
Figure 4-1 illustrates how the two branches might appear in the Service Models element hierarchy:
Figure 4-1 Service Models Element Hierarchy