3.2 Configuring Client Security Levels
You can configure the SSL VPN server to send traffic on the SSL VPN tunnel based on the level of security configured at the client machine. You can decide the categories of software that you want to be present for each level.
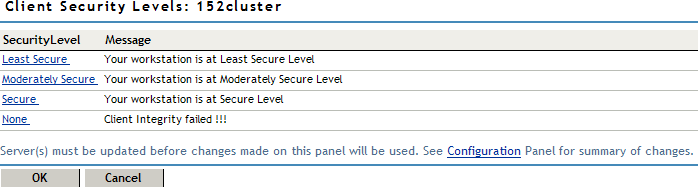
3.2.1 Client Security Levels
You can configure the following security levels:
-
Least Secure: Specifies the minimum categories of software that must be present on a client machine for the client to be at the lowest secure level. When a client is at a least secure level, you can configure the traffic policies so that the client has access to limited set of resources.
-
Moderately Secure: Specifies the categories of software that must be present on a client machine for the client to be at a moderately secure level. When a client is at a moderately secure level, you can configure the traffic policies accordingly.
-
Secure: Specifies the software categories that must be present on a client machine for the client to be secure. When a client is at a secure, the traffic policies can be configured so that the client has access to all or most of the protected resources, depending on the role of the client.
-
None: If a client does not have any of the software such as firewall or antivirus specified in the client integrity check policy, then the security level of that client is None. When a client is at this level, the SSL VPN connection is established, but the client is given access to only a minimal set of resources.
In some circumstances you cannot configure a custom security level of a client:
-
If, during the client integrity check, a client is found to have a certain level of security, then all the policies under that level as well as the policies under the lower security levels are imposed on the client. For example, if the client passes the security level check as Moderately Secure, then all the policies for this level as well as policies for Least Secure and None are imposed on the client.
-
If you change the requirements for a particular security level, the changes are applied only to new user connections. For example, a client that has established the SSL VPN connection is currently at the Secure level. You now add a new the requirement for the Secure level, so the client that is already connected at the Secure level now does not meet the requirements for the new Secure level. In this scenario, the client that is already connected continues to be connected to the server. The new policies are applicable only to new connections.
NOTE:If you want to impose the new policies for clients that are already connected, you must force the clients to reconnect by restarting the SSL VPN server.
3.2.2 Configuring a Security Level
To configure a client security level:
-
In the Administration Console, click > .
-
Select from the section.
-
Click a security level to configure it.
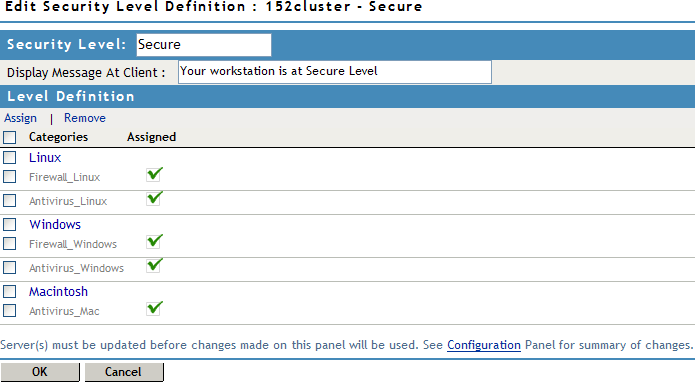
Any category that is not enabled in the
client integrity check policy appears as dimmed.
-
To assign a category for a level, select categories under each operating system, then click .
-
To remove a category for a level, select the category, then click .
-
Click to save your modifications, then click on the Configuration page.