4.5 Configuring Password Retrieval
If you have configured contracts that do not use a username and password for the credentials and you want to configure single sign-on to protected resources that require a user’s name and password, you need to configure the PasswordFetchClass to retrieve the user’s name and password. You need to create the class, then create a method from the class. The method needs to be assigned as the second method for the authentication contract that does not prompt the user for a username and password. When the Identity Server executes the contract, the PasswordFetchClass retrieves the username and password and stores them with the LDAP credentials, which makes them available for Identity Injection policies.
IMPORTANT:The PasswordFetchClass only works with eDirectory user stores.
-
In the Administration Console, click > > > > .
-
Click , then fill in the following fields:
Display name: Specify a name for the class.
Java class: Select .
The Java class path is configured automatically.
-
Click , then configure the following general properties:
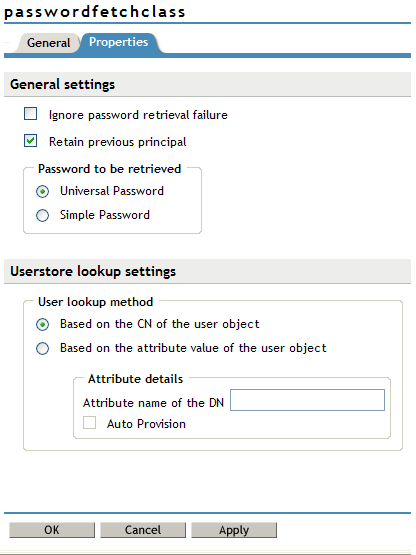
Ignore password retrieval failure: Select this option if you want users to continue with their sessions when the Identity Server can’t retrieve their passwords. If this option is not selected, users are denied access when their passwords can’t be retrieved.
Retain Previous Principal: Select this option to retain the principal obtained from the previous authentication method. If you do not select this option, then the principal will be used from the method associated with this class.
Password to be retrieved: If your users have been configured to use a universal password, select . Otherwise, select .
NOTE:Universal Password Retrieval options needs to be properly set in the configuration of the Universal Password policy, so that it allows the password to be retrieved from the User Store.
For more information on Unable to retrieve Universal Password from eDirectory using PasswordFetchClass issue, see TID 7007114
The password retrieval of the user store lookup settings are mapped based on the CN attribute value of the user object, attribute details that is based on the distinguished name to LDAP attribute. These options are added so that the password can be fetched from Active Directory. If you are not using Active Directory but eDirectory, then you use the default CN attribute of the eDirectory to map with the Active Directory user store.
-
Configure the following UserStore Lookup Settings:
Based on the CN of the user object: The CN users are mapped between two different user stores. CN is mapped with for retrieving the password from user store. For Example - Active Directory CN is mapped with eDirectory CN for retrieving the password from eDirectory user store.
Based on the Attribute value of the user object: The user names are detected and handled in LDAP attribute or DN users of the Active Directory are mapped with LDAP attribute of the eDirectory. If you select this option, then specify the attribute value in attribute details of the and enable the check box if required.
Attribute Name of the DN: Specify the attribute name of the DN. The passwordfetchclass tries fetching the password from the current user store based on the value of the LDAP attribute specified which are mapped to DN users of the Active Directory.
Auto Provision: If you enable this check box, then the passwordfetchclass tries fetching the password from LDAP attribute specified above which has the value of the DN users of the Active Directory and retrieves the password, else it prompts to log in to the eDirectory. If the log in is successful, then the LDAP attribute value gets populated with the DN user of the Active Directory. When the user is logged next time the same value is used.
-
Click .
-
Create a method for this class.
For instructions, see Section 3.3, Configuring Authentication Methods.
-
Assign the password fetch method as the second method for a contract that is using one of the following for its authentication method:
-
RADIUS. See Configuring for RADIUS Authentication.
-
X.509. See Configuring Mutual SSL (X.509) Authentication.
-
OpenID. See Configuring for OpenID Authentication.
-
Smart Card. See Configuring Access Manager for NESCM.
-
Kerberos. See Configuring for Kerberos Authentication.
-
-
Click and update the Identity Server.