3.3 Configuring Authentication Methods
Authentication methods let you associate authentication classes with user stores. You use a particular authentication class to obtain credentials about an entity, and then validate those credentials against a list of user stores.
After the system locates the entity in a particular user store, no further checking occurs, even if the credentials fail to validate the entity. Typically, the entity being authenticated is a user, and the definition of an authentication method specifies whether this is the case. You can alter the behavior of an authentication class by specifying properties (name/value pairs) that override those of the authentication class.
To configure a method for an authentication class:
-
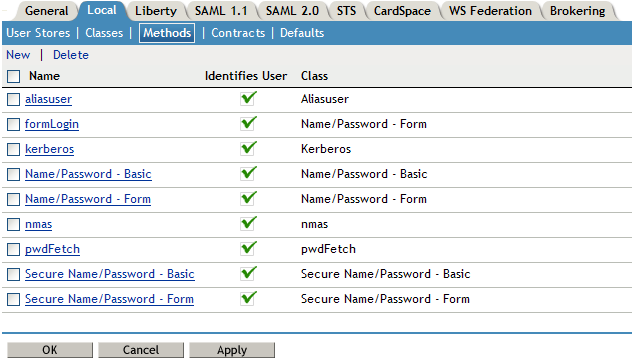
In the Administration Console, click > > > >
-
To delete a method, select the method, then click .
A method cannot be deleted if a contract is using it.
-
To modify an authentication method, click its name, or to create one, click .
-
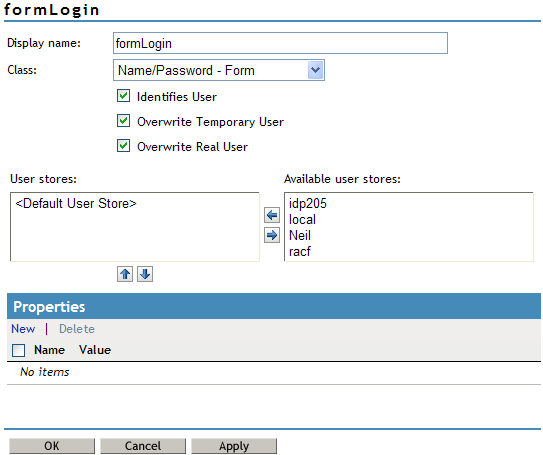
Fill in the following fields:
Display Name: The name to be used to refer to the new method.
Class: The authentication class to use for this method. See Section 3.2, Creating Authentication Classes.
Identifies User: Specifies whether this authentication method should be used to identify the user. Usually, you should enable this option. When configuring multiple methods for a contract, you might need to disable this option for some methods.
If you enable this option on two or more methods in a contract, these methods need to identify the same user in the same user store.
If you enable this option on just one method in the contract, that method identifies the user when the authentication method succeeds. The other methods in the contract must succeed, but might not authenticate the user. For example, the method that identifies the user could require a name and a password for authentication, and the other method in the contract could prompt for a certificate that identifies the user’s computer.
Overwrite Temporary User: If you select this check box, then the temporary user credentials profile got form previous authentication method in the same session will be overwritten with real user credentials profile got from this authentication method.
Overwrite Real User: If you select this check box, then the real user credentials profile got form previous authentication method in the same session will be overwritten with real user credentials profile got from this authentication method.
-
Add user stores to search.
You can select from the list of all the user stores you have set up. If you have several user stores, the system searches through them based on the order specified here. If a user store is not moved to the list, users in that user store cannot use this method for authentication.
<Default User Store>: The default user store in your system. See Section 3.5, Specifying Authentication Defaults.
-
(Optional) Under Properties, click , then fill in the following fields:
Property Name: The name of the property to be set. This value is case sensitive and specific to an authentication class. The same properties that can be set on an authentication class can be set on the method.
You can use the method properties to override the property settings specified on the authentication class. For example, you might want to use the authentication class for multiple companies, but use a slightly different login page that is customized with the company’s logo. You can use the same authentication class, create a different method for each company, and use the JSP property to specify the appropriate login page for each company.
For information on the available properties for the basic and form classes, see Section 3.2.2, Specifying Common Class Properties
The Radius classes have the following additional properties that can be set on the method:
-
RADIUS_LOOKUP_ATTR: Defines an LDAP attribute whose value is read and used as the ID is passed to the RADIUS server. If not specified, the user name entered is used.
-
NAS_IP_ADDRESS: Specifies an IP address used as a RADIUS attribute. You might use this property for situations in which service providers are using a cluster of small network access servers (NASs). The value you enter is sent to the RADIUS server.
Property Value: The values associated with the field.
-
-
Click .
-
Continue with Section 3.4, Configuring Authentication Contracts.
To use a method for authenticating a user, each method must have an associated contract.