3.2 External Services Methods
Operations Center supports the following methods using the external I&A option:
-
Windows* 2000 Active Directory*
-
iPlanet
-
OpenLDAP
-
RACF
-
Other LDAP-enabled directory services
Review the following for logging and configuring information:
3.2.1 Logging in Using External Services
When you use the external I&A option, the Operations Center administrator can configure Operations Center to use SSL when communicating with LDAP for external identification and authentication. This ensures that credential data transmitted between the Operations Center server and LDAP is secured through SSL’s encrypted communication protocol.
Figure 3-2 Secured Communication Mode Between Operations Center and LDAP

With external I&A, ACL data is stored in a binary file on the Operations Center server. Usernames and passwords are stored in LDAP.
With this method, users are required at session startup to enter their LDAP user names and passwords to access the Operations Center server. This eliminates the need to learn multiple authentication mechanisms or to remember multiple usernames and passwords. LDAP usernames and passwords are leveraged by Operations Center for authenticating users’ access to Operations Center and for assigning access to information within the Operations Center environment.
With this method, credentials are handled differently, depending on whether the LDAP connection is configured to leverage SSL. If SSL is not leveraged, the user’s password is decrypted and passed in clear text to the external LDAP system for identification and authentication.
Figure 3-3 LDAP Connection That Does Not Use SSL

If SSL is leveraged, the user’s password and other credentials are encrypted and passed through to the external LDAP system for identification and authentication.
Figure 3-4 LDAP Connection That Uses SSL

Upon successful authentication, users are allowed access to the Operations Center environment based on their assigned levels of access, as defined in the Operations Center access control lists.
3.2.2 Configuring LDAP Authentication
Operations Center can be configured to use LDAP for external authentication. LDAP authenticates users by comparing the user ID with the uid parameter in the LDAP directory. The LDAP server returns a distinguished name (DName), which the Operations Center server uses with the user password to perform an LDAP bind operation. If binding with the LDAP server is successful using the returned DName and user-provided password, the user is authenticated and allowed to log in. If the specified user ID does not exist in the LDAP directory, but does exist in Operations Center software (such as admin), the specified user is authenticated through the standard ACL component.
When using an external I&A option, the Operations Center administrator can configure Operations Center to use SSL when communicating with LDAP for external identification and authentication. This ensures that credential data transmitted between the Operations Center server and LDAP is secured through SSL’s encrypted communication protocol.
Performing a One Time Import of LDAP Users from an LDAP Directory Server
LDAP is a TCP/IP protocol for accessing online directory services that can be used to access a stand alone LDAP directory service. An LDAP directory entry is a collection of attributes identified by a distinguished name, such as a unique user name.
To enable LDAP authentication, you import LDAP users from an LDAP directory into the Operations Center server by using the admin account. User accounts can be specified that do not exist in the LDAP directory. These non-LDAP accounts are authenticated through the standard ACL component.
When users are imported from the LDAP directory to the Operations Center server, corresponding user accounts are created with read-only attributes. These users can be treated like all other users, can have ACL and other permissions, and can be assigned to groups, and so on.
To perform a one-time import of LDAP users:
-
In the pane, expand the root element > .
-
Right-click and select to display its dialog box:
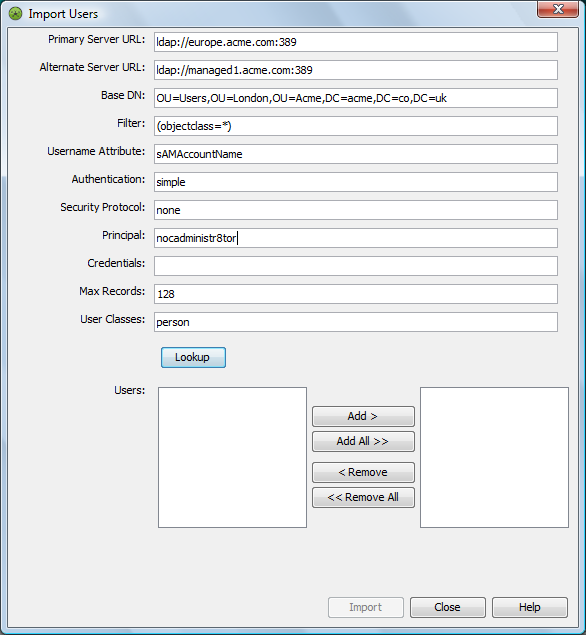
-
Configure the following required properties for authentication settings:
Primary Server URL: The LDAP server URL address to which the Operations Center server connects. An example of the LDAP URL is:
ldap://acmecorp.acme.com:389
Base DN: The distinguished name (DName) for the root naming context. For example, if your server has the root naming context, dc=example, dc=com, then specify the Base DN property for this value.
An example of the Base DN is ou=Acme Corp, dc=acme, dc=com. The organizational unit where the records reside is specified as ou=Acme Corp. For example, define an RDN as: ou=nocUsers, ou=Engineering.
-
Configure the following optional settings:
Alternate Server URL: An alternate LDAP server URL address to which the Operations Center server connects if there is a problem with the Primary Server URL.
Filter: A filter string to use during record lookup. The default filter is (objectclass=*).
Username Attribute: The directory entry attribute that is mapped to the user (login) name. The default value is uid.
For RFC‑2207 using inetOrgPerson (such as Sun* iPlanet Directory Server 5.1), enter uid.
For Microsoft Active Directory, specify the SAMAccountName.
Authentication: The level of security to use for authentication. Specify one of the following levels (default is simple):
-
None: No LDAP authentication is used.
-
Simple: Uses the server’s fully qualified DName to authenticate users; transmits user passwords in clear text. Using simple LDAP authentication within an encrypted channel can protect passwords.
-
Strong: The server uses a certificate and private key to communicate with other servers. With this level, no transmission of passwords is required, and no sensitive data is exchanged between servers until each has verified the other’s identity by using the certificates.
Security Protocol: The security protocol to use for authentication. Use a security protocol such as SSL.
Principal: The identity of the principal that authenticates the caller to the service. The format of this property depends on the authentication scheme. For example, one valid format is:
uid=Manager, dc=mosol, dc=com
Credentials: The credentials of the principal that authenticates the initial context of the service. The value of this property depends on the authentication scheme. For example, the value can be a hashed password, a clear-text password, a key, or a certificate.
Max Records: The maximum number of user records to access during lookup.
User Classes: A comma-delimited list of classes associated with imported users.
-
-
Click .
Operations Center searches the specified LDAP server for all the records specified, using the Base DN and Username Attribute values. For each record found, a user entry displays in the list.
For example, if the Base DN is dc=acme, dc=com, ou=Acme Corp, and the User Attribute is uid, a search is conducted for records of all users that have the user attribute uid under the directory object ou=NetIQ Inc, dc=acme, dc=com.
-
To add users, select the users in the left list and then click .
The users are imported to the Operations Center server and display in the right list.
-
(Optional) To delete users previously added, select the users in the right list and click .
The users are removed from the right list.
-
Click .
The records are imported one at a time for each user listed in the right pane of the Import Users dialog box.
Scheduling Regular Import and Maintainance of LDAP Users from an LDAP Directory Server
LDAP user groups allow you to import LDAP users and automatically maintain the user accounts using regularly scheduled look up queries to the LDAP directory server.
A job schedule is set for each LDAP user group defintion that runs the query for the LDAP look up procedure. The following logic applies to user profiles imported from an LDAP server:
-
For each user returned, a user account with real-only attributes is created under . These users can be treated like all other users, can have ACL and other permissions, and can be assigned to groups, and so on.
-
If a user is not returned by the LDAP look up, the user is removed from the LDAP user group; and the user profile is deleted unless the user is a member of another user group.
-
If an LDAP user group is converted from an LDAP imported group to a standard user group, all LDAP users are deleted unless the LDAP user is selected as a member of the group or is a member of another group.
To schedule the import of LDAP users using LDAP Groups:
-
In the pane, double-click the root element and .
-
Right-click and select .
The dialog box opens. Existing users and groups display in the of list.
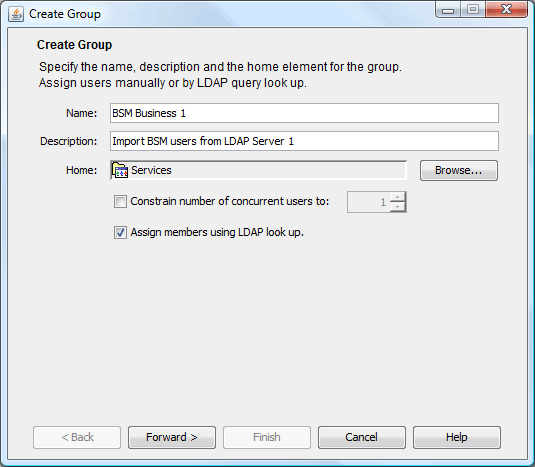
-
Type the new group name in the field.
The
 symbol identifies required fields.
symbol identifies required fields.
-
Type a description for the group in the field.
-
Click next to the field to select a root element for group users.
-
(Optional) To restrict the number of users in the group who can concurrently log in to Operations Center software, select and type the maximum number of concurrent users.
-
To import a list of users using an LDAP connection, select .
-
Click .
-
Do one of the following:
-
Select an existing LDAP Connection from the drop-down list.
-
Click to define a new LDAP Connection.
-
Click after selecting an existing LDAP Connection to view or edit the properties.
-
-
Specify the top levels of the LDAP directory tree to search in the field.
Define the Base DN as derived from your company’s DNS domain components. For example, BSMExternal.Users
CN=BSMExternal,CN=Users,DC=com
-
Customize the LDAP search string in the field.
Use an LDAP expression to specify the filter. For example, the following looks for all objects where Department, Company, or Description is Sales:
(|(department=Sales)(company=Sales)(description=Sales))
-
Specify the attribute from the LDAP server to create the User account name in the field.
-
Specify maximum number of records to return in the field.
-
Specify a comma delimited list of the object classes to search in the field.
-
Click to test the connection. A list of users is returned if successful.
HINT:If Operations Center is slow to return results, reduce the value for Max Records. After the test is complete, return the value to the desired maximum number of records for the LDAP Query.
-
Click to create and schedule a job for the LDAP query that updates the user list. By default the schedule is set to run once a day using the create time.
To edit the schedule, do the following:
-
Click .
-
Adjust the schedule as desired.
LDAP Connections use Job Scheduling. For more information on schedules, see
Scheduling Jobs
in the Operations Center 5.5 Server Configuration Guide . -
Click .
-
-
Click .
The new group is added to in the root and users are imported under.
If a problem arises during the user account creation process, an error dialog box displays and the errors are logged to the log file.
If you are familiar with NOC Script, you can use the SetGroupNames function to change a user’s group membership. For instructions, see the Operations Center 5.5 Scripting Guide.
To edit an LDAP User Group, see Section 2.6.2, Editing a Group.
Maintaining LDAP Connections
Connection information, for each LDAP Server used to import users, is maintained by LDAP connection defintions under > .
While LDAP Connection definitions are often created as part of the process of creating an LDAP user group, they can be created and edited directly from the LDAP connection definition:
NOTE:Updates to the settings for an LDAP Connection defintion are automatically leveraged by all LDAP User Groups set for that LDAP server. Likewise, an LDAP connection cannot be deleted if it is used by one or more LDAP User Groups.
Creating an LDAP Connection
To create an LDAP Connection:
-
In the pane, double-click the root element > .
-
Right-click and select .
The dialog opens.
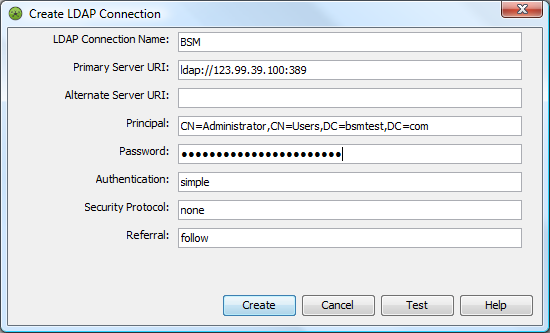
-
Specify the name of the LDAP Connection defintion in the field.
-
Specify the fully qualified address for the Operations Center server to connect to in the field.
-
(Optional) Specify an alternate LDAP server URL address to which the Operations Center server connects if there is a problem with the Primary Server URI. the field.
-
Specify the identity of the principal that authenticates the caller to the service. in the field. The format of this property depends on the authentication scheme. For example, one valid format is:
UID=Manager,DC=NetIQ,DC=com
-
Specify the password for the LDAP server connection in the field.
-
Specify one of the following levels of security to use for authentication in the field:
-
None: No LDAP authentication is used.
-
Simple: Uses the server’s fully qualified DName to authenticate users; transmits user passwords in clear text. Using simple LDAP authentication within an encrypted channel can protect passwords.
-
Strong: The server uses a certificate and private key to communicate with other servers. With this level, no transmission of passwords is required, and no sensitive data is exchanged between servers until each has verified the other’s identity by using the certificates.
-
-
Specify the type of security protocol to use for authentication in the field. Use a security protocol such as SSL
-
Specify one of the following to indicate how requests are redirected from one LDAP server to another if there is more than one user registry existing on multiple servers or domains in the field:
-
ignore: Ignores referrals.
-
follow: Follows any referrals.
-
throw: Logs a error for each referral.
-
-
Click to test the connection.
-
Click .
Editing an LDAP Connection
To edit an LDAP connection used by LDAP User Groups:
-
In the pane, double-click the root element > > .
-
Right-click the desired LDAP connection, and select .
-
Click to open the LDAP Connection pane.
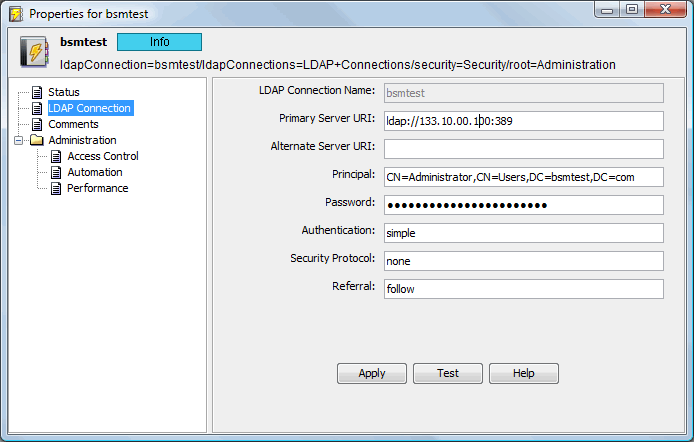
-
Modify the connection properties as desired.
-
Click to test the LDAP server connection.
-
Click to save the changes.
All user groups using the LDAP Connection are automatically updated.
Using iPlanet Server for LDAP Configuration
If you are using Sun’s iPlanet Directory Server for LDAP configuration, simple authentication must be used. The admin account is not authenticated through an iPlanet LDAP user account, because it must be authenticated through Operations Center security. For more information on iPlanet, see the Sun Web site.
Configuring Case Sensitivity Settings for LDAP Authentication
By default, the LDAP authentication process used to match and authenticate user accounts is case-sensitive, meaning the user name must be matched exactly. Update the Formula.custom.properties file to perform an additional case-insensitive search when an exact match is not found.
To configure LDAP Authentication to use a case-insensitve search for user accounts:
-
In a text editor, open the Operations_Center_install_path/NOC/config/Formula.custom.properties file.
For more information about the Formula.custom.properties file, see
Making Custom Changes
in the Operations Center 5.5 Server Configuration Guide. -
Add the following property:
Server.allow.ldap.caseinsensitive=true
-
Stop and restart the Operations Center server for the changes to take effect.
Using Log and Trace Files to Troubleshoot LDAP
See the Operations Center 5.5 Server Configuration Guide for information about configuring logging levels.
To activate LDAP logging, set the log4j.category.Server.DirectoryService category to a log level in the /OperationsCenter_install_path/config/Formula.custom.properties file.
To activate LDAP logging for the Operations Center server session, enter Server.DirectoryService in the dialog box.