3.1 Creating the Driver in Designer
You create the Sungard Banner driver by importing the driver’s configuration file and then modifying the configuration to suit your environment. After you have created and configured the driver, you need to start it.
3.1.1 Installing the Current Driver Packages
The driver packages contain the items required to create a driver, such as policies, entitlements, filters, and Schema Mapping policies. These packages are only available in Designer and can be updated after they are initially installed. You must have the most current version of the packages in the Package Catalog before you can create a new driver object.
To verify that you have the most recent version of the driver packages in the Package Catalog:
-
Open Designer .
-
In the toolbar, click >
-
Click to update the packages or click if the packages are up-to-date.
-
In the Outline view, right-click the Package Catalog.
-
Click
-
Select any Sungard Banner driver packages
or
Click to import all of the packages displayed.
By default, only the base packages are displayed. Deselect to display all packages.
-
Click to import the selected packages, and then click in the successfully imported packages message.
-
After the current packages are imported, continue with section,Section 3.1.2, Installing the Driver.
3.1.2 Installing the Driver
-
In Designer, open your project.
-
Right-click the driver-set where you want to configure the Sungard Banner driver, select and then . In the Driver Base Package Configuration screen, scroll down to find the Banner Base package. Click the box next to
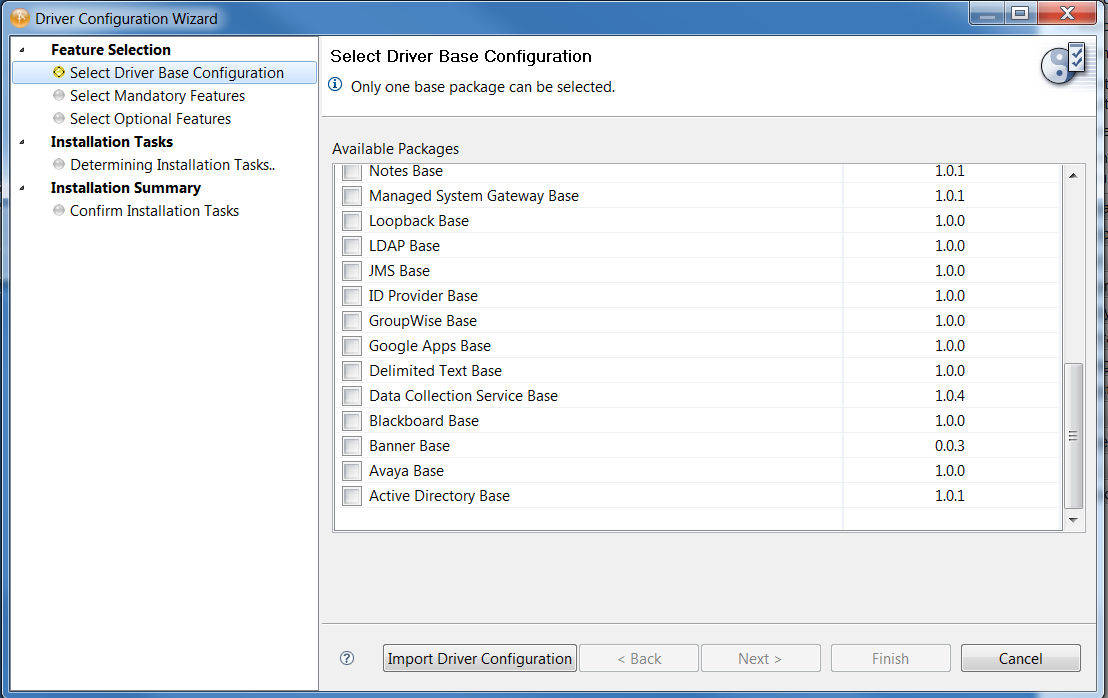
-
Select then click .
-
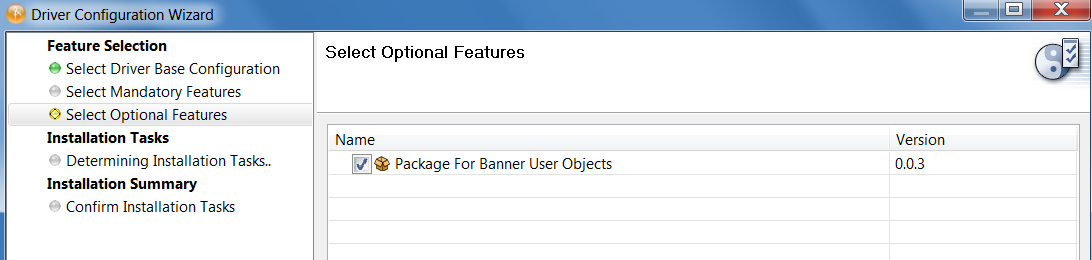
Select the optional features to install for the Sungard Banner driver.
By default is selected as expected.
-
Select the optional Sungard Banner User Package.
-
Click
-
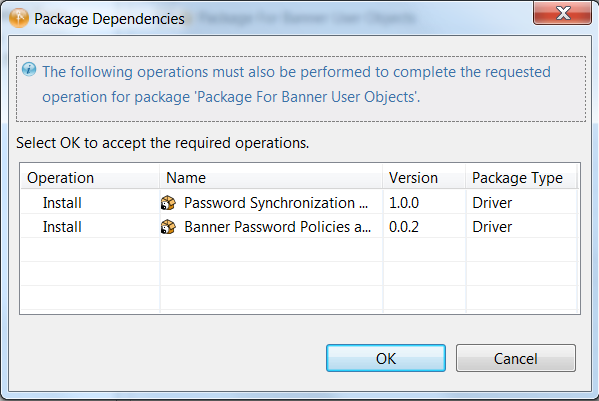
(Conditional) If there are package dependencies for the packages you selected to install, you must install them to install the selected package. Click to install package dependencies.
There will be mutable instance of this; one for each option selected.
-
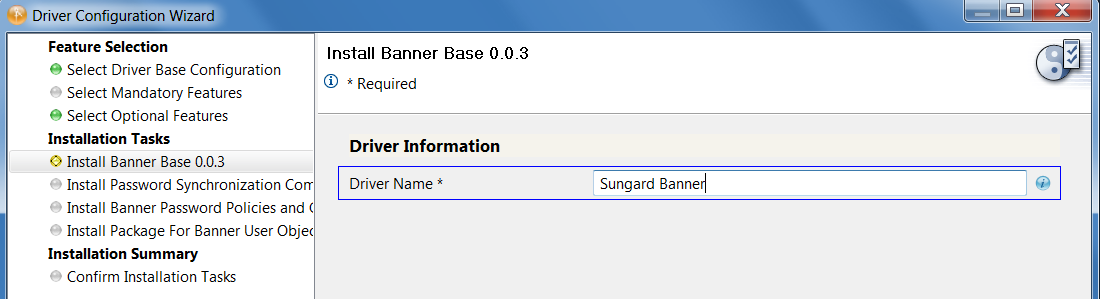
On the Install Sungard Banner Base page, specify a name for the driver that is unique within the driver set, then click .
-
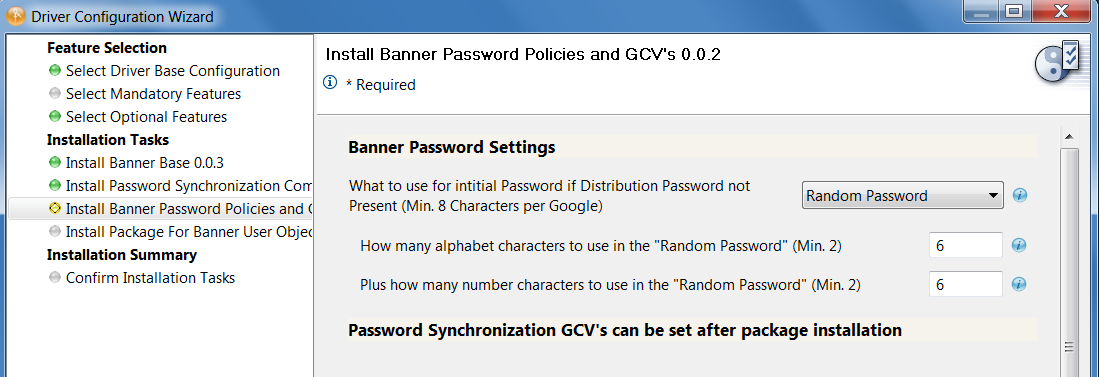
Set Banner Password Settings to configure how new user passwords are generated.
-
Select to have the password policy generate a random password. Select the number of letters and the number of digit characters to be included in the password.
-
Select to use the value of an attribute on the user as the password. The attribute name is selected from the eDirectory namespace.
Map a UDCIdentity attribute or BEIS extension attribute to an eDirectory attribute to support this policy. Ensure that the eDirectory attribute is entered in the drver filter as Notify to prevent the password from being written to the eDirectory attribute.
-
-
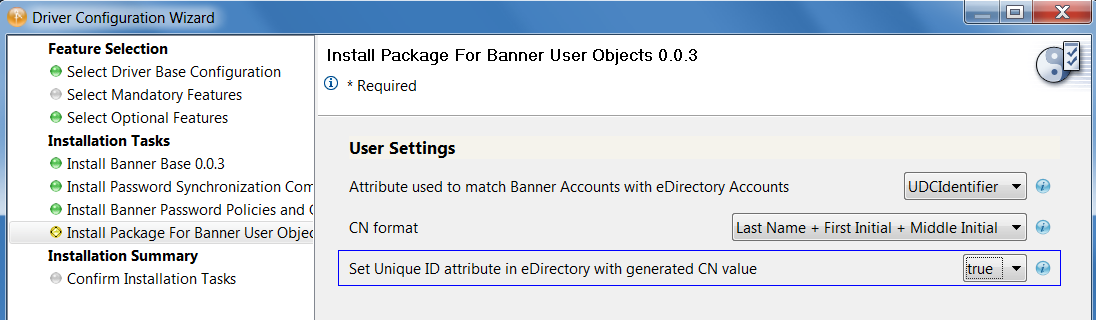
Configure the settings for User objects:
-
Attribute used to match Banner Users with eDirectory Users: Select the attribute to use as the matching attribute.
-
UDCIdentifier: Select this UDCIdentifier to use Banner’s unique object ID as the matching value.
-
CN: Select to use the CN as the matching attribute.
-
-
CN Format: CN Format lets you select from a set of predefined patterns for constructing the new user’s CN.
-
UDCIdentifier
-
First Initial + Last Name
-
First Name + Last Initial
-
First Name + Last Name
-
First Initial + Middle Initial + Last Name
-
Last Name + First Initial + Middle Initial
-
-
Set Unique ID attribute in eDirectory with generated CN value: Setting this to causes the generated CN value to also be stored in the Unique ID attribute.
-
-
Review the Summary.
-
Select .
There is no screen during import to set authentication information. The Sungard Banner driver requires separate server and authentication information for each channel.
3.1.3 Configuring the Driver
After importing the driver configuration file, you need to configure the driver before it can run.
-
There are many settings that can help you customize and optimize the driver. The settings are divided into categories such as Driver Configuration, Engine Control Values, and Global Configuration Values (GCVs). Although it is important for you to understand all of the settings, your first priority should be to review Section A.0, Driver Properties . The Driver Parameters and the Global Configuration Values let you configure the Sungard Banner login information and security credentials, and other parameters associated with the Publisher channel. These settings must be configured properly for the driver to start and function correctly. If you do not have the Driver Properties page displayed in Designer:
-
Open your project.
-
In the Modeler, right-click the driver icon or the driver connection, then select .
-
Make any desired changes, then click to save the changes.
-
After the driver is created in Designer, it must be deployed to the Identity Vault. Proceed to Section 3.1.4, Configuring Driver Parameters
3.1.4 Configuring Driver Parameters
The panel contains driver-specific configuration.
Driver Options
The Sungard Banner driver does not use any Driver Options. This panel is intentionally blank. Continue with Subscriber Options
Subscriber Options
-
URL of the remote Sungard Banner server: Specify the IP address or URL of the BEIS listener.
Example 3-1 http://10.10.1.7:4041
If you are configuring the driver to use SSL, the URL must contain a DNS name. For example: https://prod.bannerservice.com:4041
-
Authentication ID: Enter the authentication ID the driver should use when authenticating to the BEIS listener.
-
Authentication Password: Enter the password corresponding to the authentication ID.
-
Proxy host and port: When a proxy host and port are used, specify the host address and the host port. For example: 192.10.1.3:18180. Choose an unused port number on your server. Otherwise, leave this field blank.
After completing these configuration tasks, continue with Publisher Options
Publisher Options
-
Listening IP Address and Port: Specify the IP address of the server where this driver is installed and the port that this driver listens on as an SPML Server. You can specify 127.0.0.1 if there is only one network card installed in the server. Choose an unused port number on your server. For example: 127.0.0.1:18180. The driver listens on this address for SPML requests, processes them, and returns a result.
-
Require Authentication: Select to configure authentication information required by the Publisher channel.
-
Authentication ID: Specify the Authentication ID to validate incoming SPML requests.
-
Authentication Password: Specify the Authentication password to validate incoming SPML requests.
-
Accept HTTPS Connections: Select to enable HTTPS connections.
-
KMO Name: When this server is configured to accept HTTPS connections, this is the KMO name in eDirectory. The KMO name is the name before the ' - ' in the RDN. Leave this field blank when a keystore file is used or when HTTPS connections are not used.
-
Keystore File: When this server is configured to accept HTTPS connections, this is the path and the name of the keystore file. For example: C:\security\keystore. Leave this field blank when a KMO name is used or when HTTPS connections are not used.
-
Keystore Password: When this server is configured to accept HTTPS connections, this is the keystore file password. Leave this field blank when a KMO name is used or when HTTPS connections are not used.
-
Server Key Alias: When this server is configured to accept HTTPS connections, this is the key alias. Leave this field blank when a KMO name is used or when HTTPS connections are not used.
-
Server Key Password: When this server is configured to accept HTTPS connections, this is the key alias password (not the keystore password). Leave this field blank when a KMO name is used (see above) or when HTTPS connections are not used.
-
Content Type: The HTTP request header is set to this value on publisher results that are sent back to the requester.
-
Heartbeat Interval: Specify the length of time in seconds the between heartbeats emitted by the Sungard Banner driver’s Publisher channel.
After completing these configuration tasks, continue withGlobal Configuration Values (GCVs)
Global Configuration Values (GCVs)
The GCVs are defined in Table A-5.
After completing these configuration tasks, continue with Section 3.1.5, Deploying the Driver.
3.1.5 Deploying the Driver
After the driver is created in Designer, it must be deployed into the Identity Vault.
-
In Designer, open your project.
-
In the Modeler, right-click the driver icon or the driver connection, then select > .
-
Read through the deployment summary, and then click .
-
Read the success message, and then click .
-
Click to assign rights to the driver.
The driver requires rights to objects within the Identity Vault. Create a user in eDirectory for the driver to use. Assign that user administrative rights to the objects that it will need to manage objects in eDirectory.
Setting the Driver object’s Security Equivalence directly to the admin user is not recommended. Also, creating a new user for the driver and setting the new user object’s Security Equivalence to the Admin user is not recommended. The best practice is to assign specific administrative rights as needed by the driver to a user object created for the driver.
-
Click , then browse to and select the object with the correct rights.
-
Click twice.
-
-
Click to exclude users that should not be synchronized.
-
Click
3.1.6 Extending the Schema
Extending the schema is done to synchronize the identity information of user provisioning in Sungard HE in the existing eDirectory class USER, which has been modified to add the following attributes:
|
Attribute Name |
Definition |
Syntax |
Type |
|---|---|---|---|
|
udcMiddleName |
Stores the middle initial, or part of the middle name. |
CASE_IGNORE_ STRING |
Single-valued attribute. 8 characters are stored for this attribute. |
|
udcGender |
Stores the gender: male, female, unknown. |
CASE_IGNORE_ STRING |
Single-valued attribute. |
|
udcBirthDate |
Stores the birthdate: mmddyy |
CASE_IGNORE_ STRING |
Single-valued attribute. |
|
udcTaxID |
Stores a number. This could be the Social Security number. |
CASE_IGNORE_ STRING |
Single-valued attribute. |
|
udcIdentifier |
A unique key to identify the individual in the Sungard system. The driver uses this as the association key to facilitate using AccessManager to secure Sungard’s Web applications. |
CASE_IGNORE_ STRING |
Single-valued attribute. |
|
udcInstitutionalRoles |
Role information from Sungard HE. |
CASE_IGNORE_ STRING |
Multi-valued attribute. |
|
udcHomeSA |
Home street address |
CASE_IGNORE_ STRING |
Single-valued attribute |
3.1.7 Understanding Institutional Roles
Sungard provides access to applications and data by the roles applied to the people in the higher education institution. Any person might have a number of roles. For example, a university student might also be a staff member. Sungard provides 40 roles and also allows the users to add their own roles. The following list indicates some of the roles that Sungard provides:
-
PROSPECTIVE
-
PROSPECTIVESTUDENT
-
APPLICANT
-
INSTITUTIONACCEPT
-
APPLICANT ACCEPT
-
STUDENT
-
ALUMNI
-
FRIENDS
-
STAFF
-
DEVELOPMENTOFFICER
-
FINANCE
-
FACULTY
-
BANNERINB
See the Sungard HE Banner Identity Handbook for a complete list of Sungard roles, their descriptions, and possible uses.
Role Attributes
|
Role |
Description |
|
|---|---|---|
|
Role Name |
Specifies the name of the Sungard Role. |
Required |
|
Context |
The name of the Sungard component or system that created the role. Sungard always sets Context to INTCOMP. |
Optional |
|
Institution Name |
If present, it identifies the institution for which this role applies. |
Optional |
How Institutional Roles Work
Sungard HE does not delete users from the system. Instead, roles are added to and removed from users to represent their access rights. A user with no roles has no access to Sungard applications or resources. Access to resources is based on the presence of roles. Therefore, the driver synchronizes all Role information to the udcInstitutionalRoles attribute in the Identity Vault. For each XML document Sungard sends to the driver Publisher channel, a complete list of the current roles on that user is provided. The driver publishes a <remove-all-values> command to clear the udcInstitutionalRoles attribute before publishing the new list of roles it received from Sungard HE.
How Roles are Stored in udcInstitutionalRoles
UdcInstitutionalRoles is a multi-valued attribute that can contain a list of roles. The three role attributes are stored in a single value, separated by semicolons. The format is: <Role Name>;<Context>;<Institution Name>.
Role Name is a required attribute. Context is an optional attribute. It is delimiting. A semicolon is present even if the attribute is empty. Institution Name is also an optional attribute.
Example 3-2 For example, given a role of BasicPerson issued from Banner at Out Of State University, the driver generates the following:
<add-attr attr-name="InstitutionRoles"> <value>BASICPERSON;Banner;OutOfStateU</value> </add-attr>
3.1.8 Starting the Driver
When a driver is first created, it is the stopped by default. Start the driver in order to begin synchronizing data between Banner and eDirectory. Identity Manager is an event-driven system, so after the driver is started, it waits for events to be sent from BEIS or eDirectory for processing.
To start the driver:
-
In Designer, select the project view.
-
Click the Sungard Banner driver.
-
Click the green start icon.