14.3 Editing Roles
You can modify all the role parameters except Level and Subcontainer. Identity Manager Dashboard allows you to edit each role separately or multiple roles at once.
Editing individual roles: To edit an individual role, select a role from the list that you want to edit. You can perform the following operations:
-
Changing the role details such as role name, description, and categories. Adding or removing role owners.
NOTE:The role owner can be a user, a group, or a container. The role owner does not automatically have the authorization to administer changes to a role definition. In some cases, the owner must ask a Role Administrator to perform any administration actions on the role.
-
Modifying the role approval and revocation process, see Changing Approval and Revocation Process.
-
Associating resources within your organization to the selected role. See, Mapping Resources to Roles.
-
Assigning the selected role to the required users in your organization. See,Assigning Roles to Users.
-
Checking the request status of the users requesting for the selected role.
-
Mapping other roles to the selected roles. See, Mapping Roles to Roles.
Editing multiple roles at once: You can edit multiple roles as a group instead of requiring you to repeat those actions on each role individually. Select the roles you want to manage from the list of roles. You can change Categories, Owners, and Approval Details for the roles you selected. Also, you can Append or Overwrite values for Categories and Owners for the selected roles. Append option allows you to add values without altering the existing entries. Overwrite option replaces the values that are entered for the existing values.
For more information, see Changing Approval and Revocation Process.
Delete Roles: To delete any role from the list, select the role and click Delete.
When you instruct the User Application to delete a role, it first sets the role status to Pending Delete. The Role and Resource Service driver then notes the change of status and performs these steps:
-
Removes the resource assignments for the role
-
Deletes the role itself
The Role and Resource Service driver optimizes this process. However, the process may take some time, depending on the number of users assigned to the role, because the Role and Resource driver must ensure that it does not remove a resource from a user if they have this resource by other means.
For example, to check the status of a Permission role, perform the following steps in iManager:
-
Delete the role in User Application, for example, Email.
-
Log in to iManager.
-
In Objects tab, browse to Driver Set > User Application Driver > AppConfig > RoleConfig > RoleDefs > Level30.
-
Select the role that you have deleted in Step 1.
-
Click the nrfStatus attribute.
The value of the status is set to 15. The value 15 denotes that the role is in Pending Delete state.
When a role has the status of Pending Delete, you are unable to edit, delete, or assign the role.
What happens to existing role assignments If you delete a role that has an associated resource as well as one or more identities assigned to it, the system removes the resource assignment from each identity that has the associated resource.
NOTE:If you delete a role that has a resource assigned to it (or remove a user from the role), the system removes resource assignments for users in that role, even if those resources were first assigned directly. The reason for this is that the system assumes that the last authoritative source for a resource assignment is the controller of that resource, as illustrated by the following scenario:
-
A resource is created with an entitlement.
-
A user is assigned to the resource created above.
-
A role is created that is bound to the resource created in the first step above.
-
The same user is then assigned to the role created above.
-
The user is removed from the role.
In this situation, the user gets removed from the resource even though they had the resource assigned directly. Initially, the resource assignment is considered the authoritative source. However, when the user is assigned to a role that is associated with the same resource, the role becomes the authoritative source.
14.3.1 Changing Approval and Revocation Process
After you create a role, you can modify it to define the approval process for that role. An approver can be a user, group, container, or a specific role.
You can define the approval process for a role using one of the following options:
-
Serial Approval: Specify multiple approvers, and reorder the selected approvers to define the approval hierarchy.
-
Quorum Approval: Specify the approvers, then use the slide bar to specify the percent of those approvers that are required to grant access.
-
Custom: Specify the customized approval process from the list that you want to use. The list displays the workflows that are defined using Designer.
NOTE:You must set up this approval process in Designer. For more information, see NetIQ Identity Manager - Administrator’s Guide to Designing the Identity Applications.
If you choose None, no approvers are required for the role.
You can choose to have a revoke process or not. If Revoke Process Required is enabled, the revocation process follows the same process that is defined for role approval.
14.3.2 Mapping Resources to Roles
A role defines a set of duties for an individual, to carry the duties for the assigned role might require certain resources. For example, a Facilities Manager role should also have access to the Office printer. In this case, you can map the Office printer (resource) to the Facilities Manager role. When anyone requests for the Facilities Manager role, granting permission to the Facilities Manager role also grants an access to the Office printer.
While editing a role you can map resources to the selected role. Roles page also allows you to map resources to the role with more assistance such as:
-
View the existing resource to role mappings at a time.
-
Allows you to map resources/entitlements to role directly.
-
Search and filter roles, resources, and entitlements for mapping on the same page.
Click the  icon and map the resources to the required roles and perform the following steps:
icon and map the resources to the required roles and perform the following steps:
-
Select the role from the roles list.
-
Drag and drop the resources/entitlements that you want to map from the Available Resources and Entitlements list to Mapped Resources.
-
Specify the Mapping Description.
-
Click Apply.
The following image is an example for mapping resources to a role:
Figure 14-1 Map Resources to Role
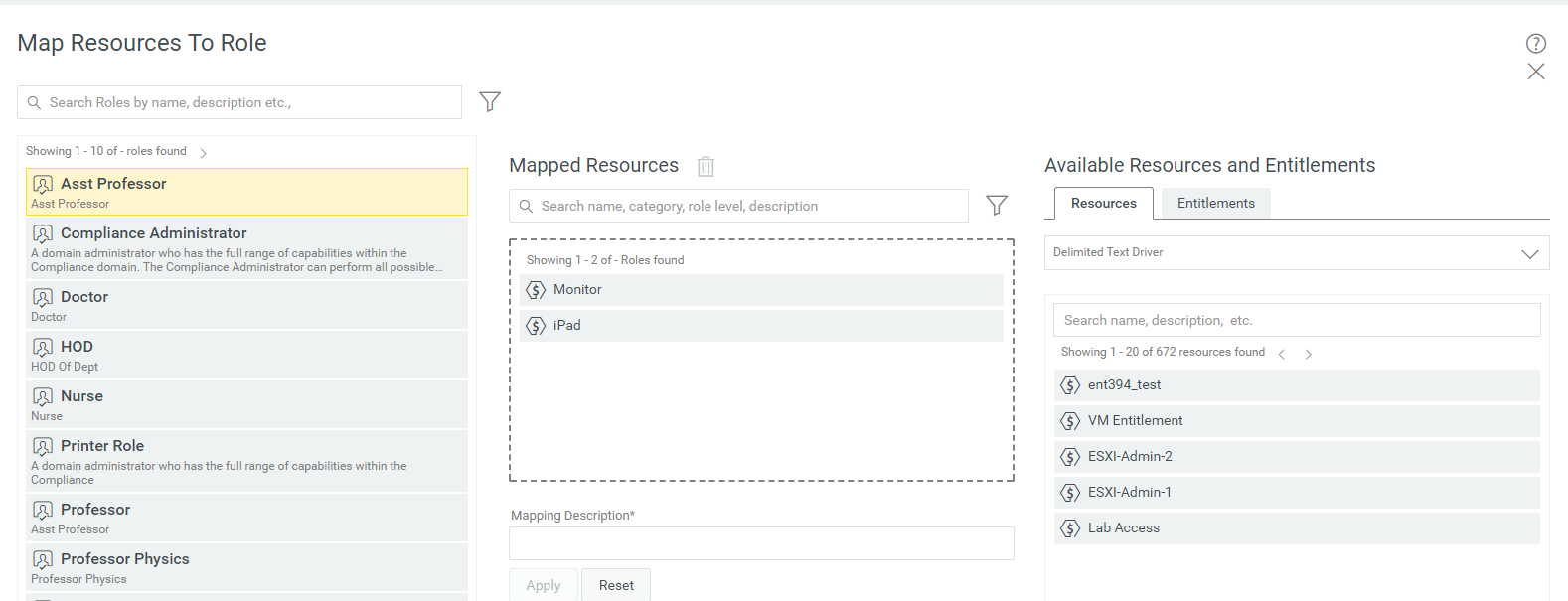
- Search Roles
-
Shows the list of roles in the organization.
- Mapped Resources
-
Shows the list of resources mapped to the selected role.
- Available Resources and Entitlements
-
Shows the list of available resources and entitlements in the organization.
14.3.3 Assigning Roles to Users
You can directly assign the selected role to any user, group, and container in your organization. While assigning roles, you can set the effective date and expiration date for this assignment.
-
Select a role that you want to assign to users.
-
In Role Assignments, Click +.
-
Specify the Initial Request Description, and mention the Recipients from the list.
NOTE:In Initial Request Description, describe the purpose of assigning a role to the mentioned users in Recipients list.
In Recipients, you can mention users, group, and container from the list.
-
(Conditional) Set the Effective Date and Expiration Date for this assignment.
If you do not set effective and expiration date, the effective date will be set to the present day and no expiry for this assignment.
-
Click Assign Role.
For more information, click ![]() on the dashboard.
on the dashboard.
14.3.4 Mapping Roles to Roles
Role levels define role hierarchy. The roles hierarchy supports three levels. Roles defined at the highest level (called Business Roles) define operations that have business meaning within the organization. Mid-level roles (called IT Roles) supports technology functions. Roles defined at the lowest level of the hierarchy (called Permission Roles) define lower-level privileges.
A higher-level role automatically includes privileges from the lower-level roles that it contains. For example, a Business Role automatically includes privileges from the IT Roles that it contains. Similarly, an IT Role automatically includes privileges from the Permission Roles that it contains.
Role relationships are not permitted between peer roles within the hierarchy. In addition, lower-level roles cannot contain higher-level roles.
You can modify the label used for each role level in the User Application by defining localized strings for the level’s Name and Description in the role configuration editor.
You can define Parent Roles and Child Roles for the selected role.
- Parent Roles
-
Roles which are higher to the selected role. These roles have all the permissions of the selected role in addition to the permissions specified for these roles.
- Child Roles
-
Roles which are lower to the selected role. The selected role has all the permissions of the child roles in addition to the permissions specified for the selected role.
A child role must have a lower role level than the parent role, and the parent role is automatically assigned the privileges assigned to the lower-level roles.
Figure 14-2 Map Roles to Roles
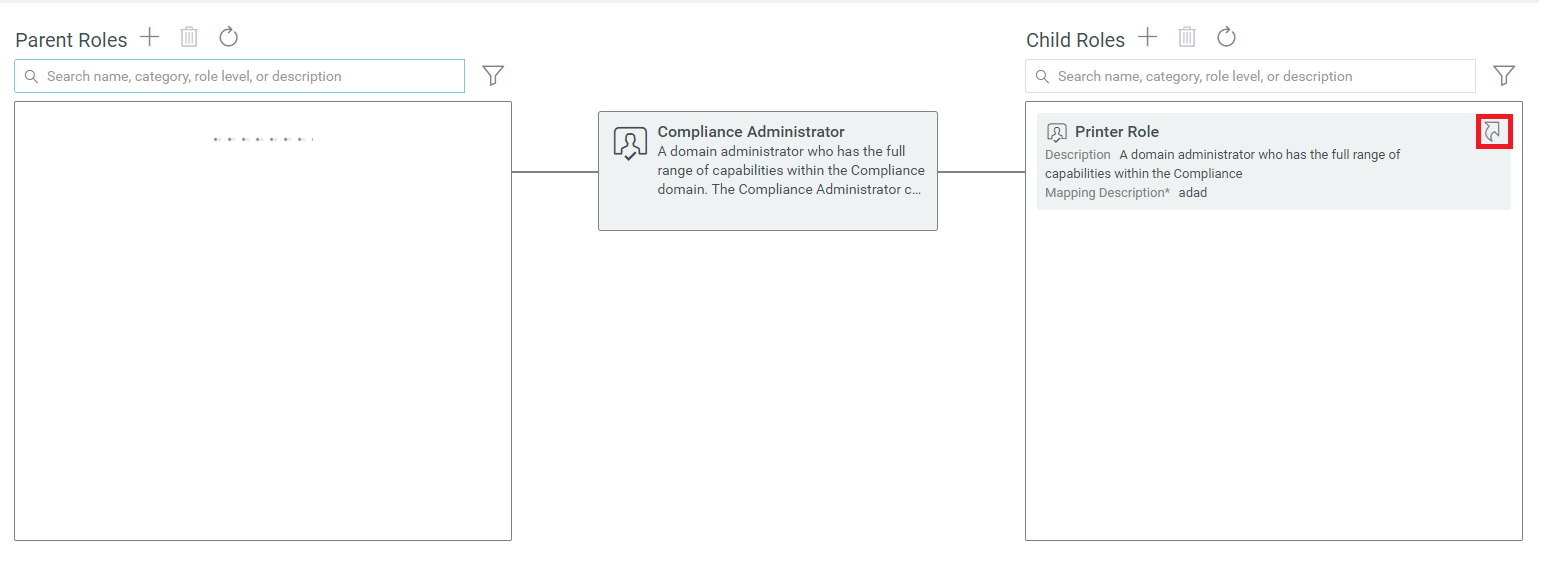
HINT:To see the role relationship of a Parent or Child Role, click ![]() on the role that you wish to see the hierarchy.
on the role that you wish to see the hierarchy.