16.1 Overview of Roles
Identity Governance enables you to manage both the technical and business roles in your organization. To enable easier management of these roles, Identity Governance assigns technical role administrators and business role administrators with separate but overlapping responsibilities.
Business roles organize people by their business function and user-based attributes to solve questions of what users should have access to because of who they are or what they need or might have an option to request without additional approval. Business roles authorize resources (permissions, technical roles, and applications) for users who are members of the business role. These authorizations also specify whether resources are to be auto-granted to users, auto-revoked from users, or should not be auto-granted and auto-revoked.
Technical roles organize lower-level permissions into sets of permissions that offer enough business value to be reviewed and assigned as a unit or requested as a unit. Technical roles are designed to limit the number of review items and surface permissions in ways that can be presented to typical non-administrator users.
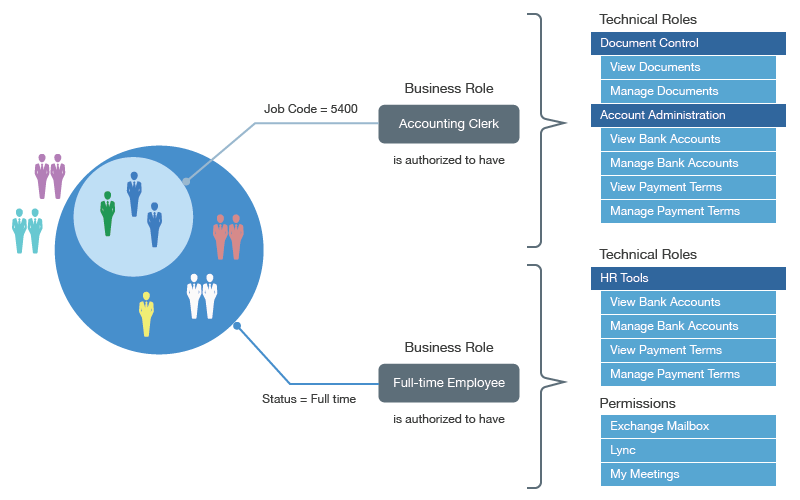
Figure 16-1 contains an example of how the different types of roles overlap. The company’s policies authorize all full-time employees to have access to the HR Tools, Exchange Mailboxes, Lync, and My Meeting. Accounting clerks are authorized to have access to Document Control and Account Administration, a technical role that the technical role administrator created in Identity Governance. When you include a user as a member of a business role of Full-time Employee and Accounting Clerk, Identity Governance authorizes the user to have any of the mandatory or optional technical roles or permissions listed for the given role. Identity Governance could potentially automatically provision mandatory permissions, while it could assign optional permissions at a later time without further approval as they have been pre-approved by the policy. This saves you time, effort, and error and enables controlled access through business roles. To understand how your entitlement assignments conform to your business policies, you can view the Role Leverage widget on the Overview page. For more information, see Viewing Entitlement Assignments Statistics to Leverage Roles.
Figure 16-1 Detailed Example of the Overlap between Business Roles and Technical Roles
NOTE:This chapter primarily discusses business role policy concepts and procedures. For information about technical roles, see Section 15.0, Creating and Managing Technical Roles.