2.2 Cloud Manager Orchestration Server Requirements
Use the requirements in this section to plan your deployment of the Cloud Manager Orchestration Server.
2.2.1 Requirements For the Orchestration Server
The network machine where you install Cloud Manager Orchestration Server software must meet the requirements in Table 2-1:
Table 2-1 Orchestration Server Requirements
|
Item |
Requirement |
|---|---|
|
Operating System |
SUSE Linux Enterprise Server 11 Service Pack 4 (SLES 11 SP 4) on the 64-bit (x86-64) architecture (Intel processor or AMD Opteron processor) |
|
Hardware |
|
|
Hostname Resolution |
The server must resolve device host names by using a method such as DNS (recommended). |
|
IP Address |
The server must have a static IP address or a permanently leased DHCP address. |
2.2.2 Port Requirements for the Orchestration Server
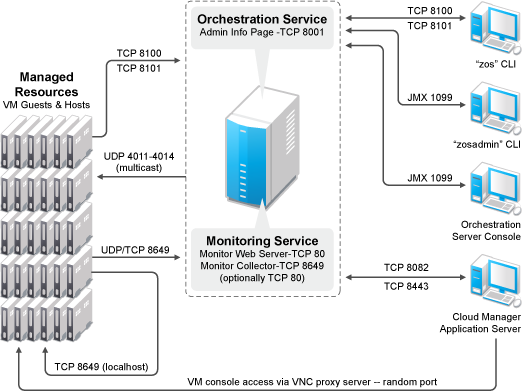
Table 2-2 identifies the ports and protocols required by the Cloud Manager Orchestration Server. Ports are configurable except where they are specified as mandatory. The Orchestration Server firewall must allow traffic for the ports (or their substitutes if you are not using the defaults). Network firewalls need to allow outgoing agent connections to TCP ports 8100 (not secure) and 8101 (secure) on the server.
Table 2-2 Port Requirements for the Orchestration Server
|
Port Number |
Protocol |
Function |
|---|---|---|
|
80 |
TCP |
(Not secure) Used for the Monitor Web Server. TCP Port 80 can be used by the Monitor Collector instead of TCP port 8649. |
|
8001 |
TCP |
Used for communication with the Administrator Information page. |
|
8100 |
TCP |
(Not secure) Used with a custom protocol for communication with the Orchestration Agent and for invoking the zos command line interface or opening the Java Developer’s toolkit. |
|
8101 |
TCP |
(Secure) Used for invoking the zos command line interface or opening the Java Developer’s toolkit by using TLS. |
|
8082 |
TCP |
(Not secure) Used by the Cloud Manager Application Server to communicate with the Cloud Manager Orchestration Server. The Cloud Manager Orchestration Web Service exposes a RESTful interface used by the Cloud Manager Application Server to communicate with the Cloud Manager Orchestration Server through TCP ports 8082 and 8443. |
|
8443 |
TCP |
(Secure) Used by the Cloud Manager Application Server to communicate with the Cloud Manager Orchestration Server. See also port 8082. |
|
8649 |
TCP and UDP |
Used by monitored systems (physical and virtual) to send metrics to the Monitoring Server. The port must be available for gmond to communicate with the Orchestration Agent. The Monitoring Server is installed on the same system as the Cloud Manager Orchestration Server. TCP 8649 is used by the Monitor Collector component of the Monitoring Server. You can alternatively use TCP port 80. TCP 8649 is used on the monitored system to communicate to the localhost. |
|
1099 |
TCP and UDP |
Mandatory. Used with RMI for invoking the zosadmin command line interface or for running the Orchestration Console. |
|
VNC ports (1000–1xxx) |
TCP |
Used by connections to VM consoles through a VNC client. Typically, this means TCP port 1000 for the first VM on a VM host, 1001 for the second, and so on. These connections go to the VM host, exposing the console on behalf of the VM. |
|
4000 |
UDP |
Used as a datagrid multicast request port and a control channel port. |
|
4011–4014 |
UDP |
Used for datagrid multicast file transfers. Enable for outbound communications. Multicast groups for datagrid multicast-based file transfers are 239.192.10.10–14. |
|
5432 |
TCP |
Used by the PostgreSQL database by default. Without an open port in the host firewall, a remote Orchestration Server cannot access the audit database. If you use a different external RDBMS with Orchestration Server, ensure that you open its ports instead. |
|
1443 |
TCP |
Used for Sentinel Syslog secure communications by default, if you configure Sentinel for integration with Cloud Manager. |
Figure 2-1 shows the relationships between the Cloud Manager components and managed resources, as well as the traffic flow between them:
Figure 2-1 Required Network Resources for the Cloud Manager Orchestration Server