1.4 Architecture
Advanced Authentication architecture is based on the following three levels of architecture:
-
Basic Architecture
For more information, see Basic Architecture
-
Enterprise Level Architecture
For more information, see Enterprise Level Architecture
-
Enterprise Architecture With A Load Balancer
For more information, see Enterprise Architecture With A Load Balancer
1.4.1 Basic Architecture
The basic architecture of Advanced Authentication is a simple configuration that requires only one Advanced Authentication server.

An Advanced Authentication server is connected to a directory such as Active Directory Domain Services, NetIQ eDirectory, Active Directory Lightweight Directory Service or other compliant LDAP directories. An Event Endpoint can be Windows, Linux or Mac OS X machine, NetIQ Access Manager, NetIQ CloudAccess, or RADIUS Client to authenticate through the RADIUS Server that is built-in the Advanced Authentication Server. For a complete list of supported events, see Configuring Events.
1.4.2 Enterprise Level Architecture
In the enterprise level architecture of Advanced Authentication, you can create several sites for different geographical locations.
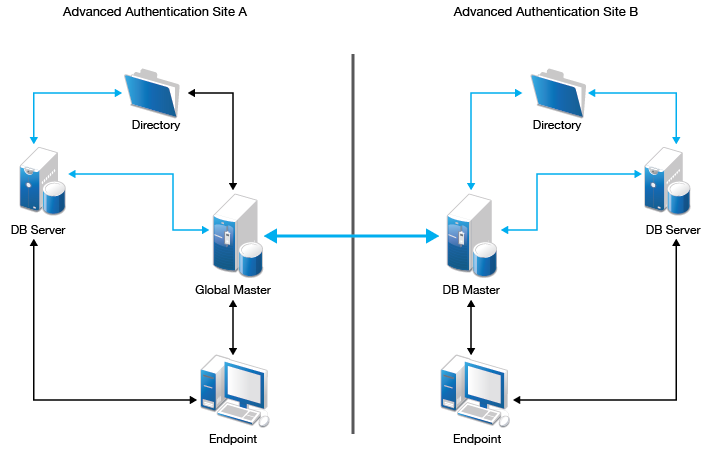
For example, the Figure 1-1 displays two Advanced Authentication sites, Site A and Site B.
Figure 1-1 Enterprise Level Architecture
-
Site A: The first site that is created for headquarters in New York. The first Advanced Authentication server of site A contains the Global Master and Registrar roles. This server contains a master database and it can be used to register new sites and servers.
-
Site B: Another site created for the office in London. The structure of site B is similar to site A. The Global Master in another site has the DB Master role. DB servers interact with the DB Master.
DB Server provides a database that is used for backup and fail-over. You can create a maximum of two DB servers per site. When the Global Master is unavailable, the DB server responds to the database requests. When the Global Master becomes available again, the DB server synchronizes with the Global Master and the Global Master becomes the primary point of contact for database requests again.
Endpoints interact with Global Master or DB Master servers. When these servers are not available, they interact with DB servers.
NOTE:DB servers connect to each other directly. If the Global Master is down, the DB servers will replicate.
A Global Master must have a connection to each of the LDAP servers. Hence in a data center with Global Master, you must have LDAP servers for all the used domains.
Master servers do not initiate a connection to the DB servers. Master servers initiate connection to Master servers only. DB servers initiate connection to the DB Master of the same site and Registrar only.
IMPORTANT:Ensure to take regular snapshots or to clone the primary site to protect from any hardware issues or any other accidental failures. It is recommended to do it each time after you change the configuration of repositories, methods, chains, events and policies, or add or remove servers in the cluster.You can convert DB server of primary site to Global Master. This requires corresponding DNS changes. Nothing can be done if Global Master and all the database servers are lost.
1.4.3 Enterprise Architecture With A Load Balancer
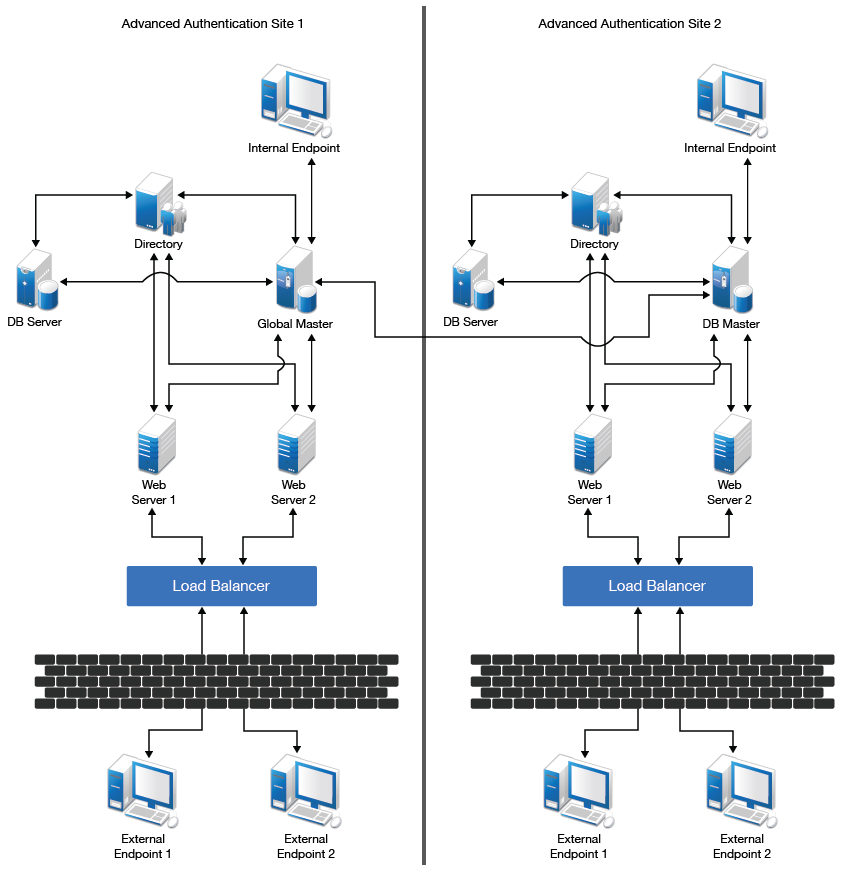
The enterprise architecture with a load balancer contains web servers and load balancers along with the components in Enterprise Level Architecture. Figure 1-2 illustrates the Enterprise architecture with a load balancer.
Figure 1-2 Enterprise Architecture with Load Balancer
-
Web Servers: Web server does not contain a database. It responds to the authentication requests and connects to Global Master. You need more web servers to serve more workload. It is not recommended to deploy more than 5-6 web servers per site.
-
Load Balancer: A load balancer provides an ability to serve authentication requests from External Endpoints. A load balancer is a third-party component. It must be configured to interact with Web servers.
WARNING:Do not place the Advanced Authentication server in Demilitarized Zone (DMZ). It is recommended to use Load Balancer to process authentication requests from the external endpoints.
For example, if the Global Master server (GMS) of a cluster goes down, the DB server of the site is promoted as the new GMS of the cluster. Here, another server is promoted as the new DB server of site A. The IP address of the new GMS remains the same as the previous GMS. For example the IP address of the old GMS is 1.1.1.1, then the IP of the new GMS will remain the same and the Load balancer is aware of this change. For information about how to restore the operations when a GMS is broken, see Restoring Operations When a Global Master Server is Broken
.
NOTE:To view an example of configuring a load balancer for an Advanced Authentication cluster, see Installing a Load Balancer for Advanced Authentication Cluster
.