4.1 Local Authentication
To guard against unauthorized access, Access Manager supports a number of ways for users to authenticate. You configure authentication at Identity Server by creating authentication contracts that Access Manager components (such as an Access Gateway) can use to protect a resource.
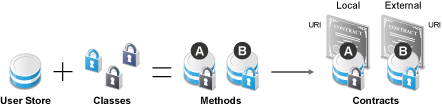
Figure 4-1 illustrates the components of a contract.
Figure 4-1 Local Authentication
-
User stores: The user directories to which users authenticate in the back-end. You set up your user store when you create an Identity Server cluster configuration. See Section 4.1.1, Configuring Identity User Stores.
-
Classes: The code (a Java class) that implements a particular authentication type (name/password, RADIUS, and X.509) or means of obtaining credentials. Classes specify how Identity Server requests authentication information, and what it must do to validate those credentials. See Section 4.1.2, Creating Authentication Classes.
-
Methods: The pairing of an authentication class with one or more user stores, and whether the method identifies a user. See Configuring Authentication Methods.
-
Contracts: The basic unit of authentication. Contracts can be local (executed at the server) or external (satisfied by another Identity Server). Contracts are identified by a unique URI that can be used by Access Gateways and agents to protect resources. Contracts are comprised of one or more authentication methods used to uniquely identify a user. You can associate multiple methods with one contract. See Configuring Authentication Contracts.
This section explains the following topics: