1.5 Setting Up Firewalls
Access Manager Appliance should be used with firewalls. Figure 1-5 illustrates a simple firewall setup for a basic Access Manager Appliance configuration.
Figure 1-5 Access Manager Appliance and Firewall
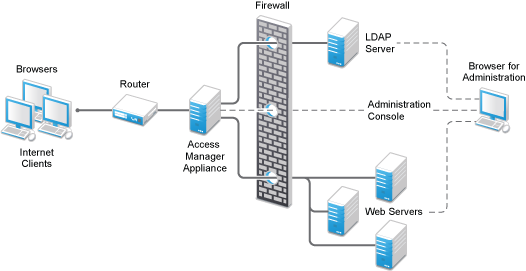
The first firewall separates the Access Manager Appliance from the Internet, allowing browsers to access the resources through specific ports. This is one of many possible configurations. This section describes the following:
1.5.1 Required Ports
The following table lists the ports that need to be opened when a firewall separates Access Manager Appliance from Internet.
With these tables, you should be able to place Access Manager Appliance of your system anywhere within your existing firewalls and know which ports need to be opened in the firewall.
|
Component |
Port |
Description |
|---|---|---|
|
NTP Server |
UDP 123 |
Access Manager components must have time synchronized else the authentication fails. We highly recommend that all components be configured to use an NTP (network time protocol) server. Depending upon where your NTP server is located in relationship to your firewalls, you might need to open UDP 123 so that the Access Manager component can use the NTP server. |
|
DNS Servers |
UDP 53 |
Access Manager components must be able to resolve DNS names. Depending upon where your DNS servers are located, you might need to open UDP 53 so that the Access Manager component can resolve DNS names. |
|
Remote Linux Administration Workstation |
TCP 22 |
If you use SSH for remote administration and want to use it for remote administration of Access Manager components, you need to open TCP 22 to allow communication from your remote administration workstation to your Access Manager components. |
|
Access Manager Appliance |
TCP 1443 |
For communication from the Administration Console to the devices. |
|
TCP 8444 |
For communication from the devices to the Administration Console. |
|
|
TCP 1289 |
For communication from the devices to the Audit server on the Administration Console. |
|
|
TCP 524 |
For NCP certificate management with NPKI. The port needs to be opened so that both the device and the Administration Console can use the port. |
|
|
TCP 636 |
For secure LDAP communication from the devices to the Administration Console. |
|
|
TCP 524 |
Required to synchronize the configuration data store. |
|
|
TCP 636 |
Required for secure LDAP communication. |
|
|
TCP 8080, 8443 |
Used for Tomcat communication. |
|
|
LDAP User Store |
TCP 524 |
Required only if the user store is eDirectory. When configuring a new eDirectory user store, NCP is used to enable Novell SecretStore by adding a SAML authentication method and storing a public key for the Administration Console. It is not used in day-to-day operations. |
|
Browsers |
TCP 8080 |
For HTTP communication from browsers to the Administration Console. |
|
TCP 8443, 2443, 2080. |
For HTTPS communication from browsers to the Administration Console. |
|
|
TCP 8028, 8030 |
To use iMonitor or DSTrace from a client to view information about the configuration store on the Administration Console. |
|
|
TCP 80 |
For HTTP communication from the client to the Access Gateway. This is configurable. |
|
|
TCP 443 |
For HTTPS communication from the client to the Access Gateway. This is configurable. |
|
|
Web Servers |
TCP 80 |
For HTTP communication from the Access Gateway to the Web servers. This is configurable. |
|
TCP 443 |
For HTTPS communication from the Access Gateway to the Web servers. This is configurable. |
NOTE:On SLES 11, you can edit this file or use YaST to configure UDP ports and internal networks.
1.5.2 Sample Configurations
Access Manager Appliance in DMZ
First Firewall
If you place a firewall between browsers and Access Manager Appliance, you need to open ports so that browsers can communicate with the Access Gateway and the Identity Server and the Identity Server can communicate with other identity providers.
See, Figure 1-5
Table 1-2 Ports to Open in the First Firewall
|
Port |
Purpose |
|---|---|
|
TCP 80 |
For HTTP communication. |
|
TCP 443 |
For HTTPS communication. |
|
Any TCP port assigned to a reverse proxy or tunnel. |
|
|
TCP 8080 |
For HTTP communication with the Identity Server. |
|
TCP 8443 |
For HTTPS communication with the Identity Server. |
|
TCP 8445 |
For HTTP Identity Provider introductions. If you do not enable Identity Provider introductions, you do not need to open this port. |
|
TCP 8446 |
For HTTPS Identity Provider introductions. If you do not enable Identity Provider introductions, you do not need to open this port. |
Second Firewall
The second firewall separates Web servers, LDAP servers, and the Administration Console from the Identity Server and the Access Gateway. You need the following ports opened in the second firewall:
Table 1-3 Ports to Open in the Second Firewall
|
Port |
Purpose |
|---|---|
|
TCP 80 |
For HTTP communication with Web servers. |
|
TCP 443 |
For HTTPS communication with Web servers. |
|
Any TCP connect port assigned to a Web server or to a tunnel. |
|
|
TCP 1443 |
For communication from the Administration Console to the devices. |
|
TCP 8444 |
For communication from the devices to the Administration Console. |
|
TCP 1289 |
For communication from the devices to the Audit server installed on the Administration Console. If you do not enable auditing, you do not need to open this port. |
|
TCP 524 |
For NCP certificate management in NPKI. The port needs to be opened so that both the device and the Administration Console can use the port. |
|
TCP 636 |
For secure LDAP communication of configuration information. |
You need to open ports on the second firewall according to the offered services.