6.1 Installing and Configuring the User Application WAR
NOTE:For WebSphere 7.0, the installation program requires the 1.6 JDK from IBM. If you use a different version, the installation procedure does not successfully configure the User Application WAR file. The installation appears to succeed, but you encounter errors when trying to start the User Application.
-
Navigate to the directory containing your installation files.
-
You must apply the unrestricted policy files to the IBM JDK. You can refer to your WebSphere documentation for a link to these files from IBM and instructions for applying them. Apply these files to your IBM JDK environment before proceeding any further with the installation. The JAR file for unrestricted policy files need to be placed in JAVA_HOME\jre\lib\security.
Without these unrestricted policy files, an error will occur that says
Illegal key size
. The root cause of this problem is the lack of unrestricted policy files, so be sure to use the correct IBM JDK. -
Launch the installer using the IBM Java environment, as shown below:
Linux or Solaris
$ /opt/WS/IBM/WebSphere/AppServer/java/bin/java -jar IdmUserApp.jar
Windows
C:\WS\IBM\WebSphere\AppServer\java\bin\java -jar IdmUserApp.jar
When the installation program launches, you are prompted for the language:
-
Use the following information to select the language, confirm the license agreement, and select the Application Server platform:
Installation Screen
Description
User Application Installation
Select the language for the installation program. The default is English.
License Agreement
Read the License Agreement, then select I accept the terms of the License Agreement.
Application Server Platform
Select WebSphere.
If the User Application WAR file is in a different directory from the installer, the installer prompts for the path to the WAR.
If the WAR is in the default location, you can click Restore Default Folder. Or, to specify the location of the WAR file, click Choose and select a location.
When you’re installing on WebSphere, you need to launch the installation program by using the IBM Java environment. If you select WebSphere as the application server, and do not use IBM’s Java to launch the installation, you will see a pop-up error message, and the installation will terminate:
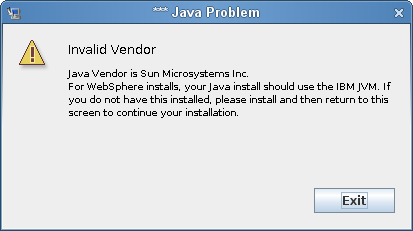
-
Use the following information to choose an install folder and configure the database:
Installation Screen
Description
Choose Install Folder
Specify where you want the installer to put the files.
Database Platform
Select the database platform. The database and JDBC driver must already be installed. For WebSphere, the options include the following:
-
Oracle
-
Microsoft SQL Server
-
IBM DB2
-
PostgreSQL
Database Host and Port
Host: Specify the database server’s hostname or IP address. For a cluster, specify the same hostname or IP address for each member of the cluster.
Port: Specify the database’s listener port number. For a cluster, specify the same port for each member of the cluster.
Database Username and Password
Database Name (or SID): For DB2, MS SQL Server, or PostgreSQL provide the name of your preconfigured database. For Oracle, provide the Oracle System Identifier (SID) that you previously created. For a cluster, specify the same database name or SID for each member of the cluster.
Database Username: Specify the database user. For a cluster, specify the same database user for each member of the cluster.
Database Password: Specify the database password. For a cluster, specify the same database password for each member of the cluster.
Database Driver JAR file: Provide the Thin Client JAR for the Database Server. This is required.
IMPORTANT:The browse button for the Database Driver JAR File field allows you to select only one (1) jar. For DB2, you must provide two (2) jars:
-
db2jcc.jar
-
db2jcc_license_cu.jar
Therefore, you can select one JAR, but will have to manually enter the second one using the correct file separator for the operating system that the install program is running on. Alternatively, you can manually enter both entries.
For example, on Windows:
c:\db2jars\db2jcc.jar;c:\db2jars\db2jcc_license_cu.jar
For example, on Solaris and Linux:
/home/lab/db2jars/db2jcc.jar:/home/lab/db2jcc_license_cu.jar
Database Administrator
This screen is pre-populated with the same username and password from the Database Username and Password page. If the database user that was specified earlier does not have enough permissions to create tables in the Database Server, then a different user ID that has the necessary rights needs to be entered.
Create Database Tables
Specify when the database tables should be created.
New Database or Existing Database
If the database that will be used is new or empty, then select the New Database button. If the database is an existing one from a previous installation, select the Existing Database button.
Test Database Connection
To confirm that the information provided in the previous screens was correct, you can test the database connection by selecting Test Database Connection.
The installer needs to connect to the database both for creating tables directly and for creating the .SQL file. If you test the database connection and it fails, you may still continue with installation. In this case, you will need to create the tables after installation, as described in the User Application: Administration Guide.
-
-
Use the following information to configure Java and Identity Manager, as well as audit settings and security.
Installation Screen
Description
Java Install
Specify the Java root install folder. The Java Install provides the path to Java based on your JAVA_HOME environment variable and gives you the option to correct it.
At this point, the Installation program also validates that the Java selected is the correct one for the Application Server selected. In addition, it validates that it can write to the cacerts in the JRE that was specified.
IDM Configuration
Application Context: The name of the application server configuration, the name of the application WAR file, and the name of the URL context. The installation script creates a server configuration and by default names the configuration based on Application name. Make a note of the application name and include it in the URL when you start the User Application from a browser.
Select Audit Logging Type
To enable logging, click Yes. To disable logging, click No.
The next panel prompts you to specify the type of logging. Choose from the following options:
-
Novell Identity Audit or Novell Sentinel: Enables logging through a N0ovell client for the User Application.
-
OpenXDAS: Events are logged to your OpenXDAS logging server.
For more information on setting up logging, see the User Application: Administration Guide.
Novell Identity Audit or Novell Sentinel
Server: If you enable logging, specify the hostname or IP address for the server. If you turn logging off, this value is ignored.
Log Cache Folder: Specify the directory for the logging cache.
Security - Master Key
Yes: Allows you to Import an existing master key. If you choose to import an existing encrypted master key, cut and paste the key into the install procedure window.
No: Creates a new master key. After you finish the installation, you must manually record the master key as described in Section 9.1, Recording the Master Key.
The installation procedure writes the encrypted master key to the master-key.txt file in the installation directory.
Reasons to import an existing master key include:
-
You are moving your installation from a staging system to a production system and want to keep access to the database you used with the staging system.
-
You installed the User Application on the first member of a cluster and are now installing on subsequent members of the cluster (they require the same master key).
-
Because of a failed disk, you need to restore your User Application. You must reinstall the User Application and specify the same encrypted master key that the previous installation used. This gives you access to the previously stored encrypted data.
-
-
If you would like to configure RBPM now, select Configure Now and click Next.
(If you are not prompted for this information, you might not have completed the steps outlined in Section 2.5, Installing the Java Development Kit.)
The default view of the Roles Based Provisioning Module Configuration panel shows these six fields:
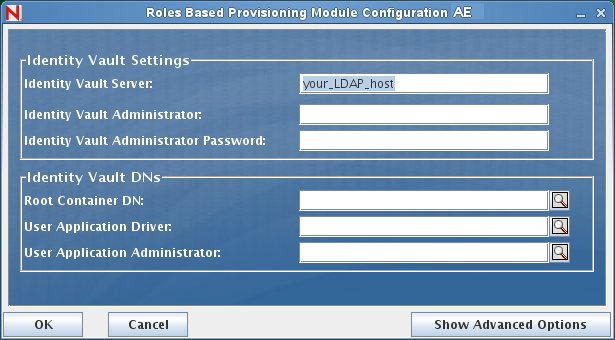
The Installation program will take the value from the Root Container DN and apply it to the following values:
-
User Container DN
-
Group Container DN
The Installation program will take the value from the User Application Administrator fields and apply it to the following values:
-
Provisioning Administrator
-
Compliance Administrator
-
Roles Administrator
-
Security Administrator
-
Resources Administrator
-
RBPM Configuration Administrator
If you want to be able to specify these values explicitly, you can click the Show Advanced Options button and change them:
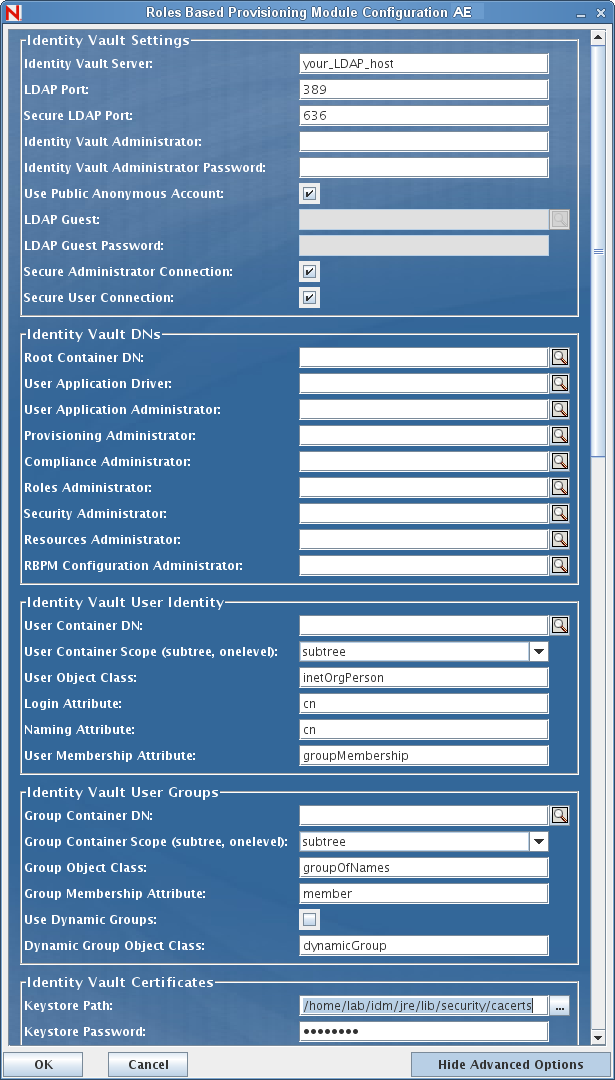
The User Application install enables you to set User Application configuration parameters. Most of these parameters are also editable with configupdate.sh or configupdate.bat after installation; exceptions are noted in the parameter descriptions.
See Section A.0, User Application Configuration Reference for a description of each option.
-
-
Use the following information to complete the installation.
Installation Screen
Description
Pre-Installation Summary
Read the Pre-Installation Summary page to verify your choices for the installation parameters.
If necessary, use Back to return to earlier installation pages to change installation parameters.
The User Application configuration page does not save values, so after you re-specify earlier pages in the installation, you must re-enter the User Application configuration values. When you are satisfied with your installation and configuration parameters, return to the Pre-Install Summary page and click Install.
Install Complete
Indicates that the installation is finished.
6.1.1 Viewing Installation Log Files
If the installation issued errors or warnings, review the log files to determine the problems:
-
Identity_Manager_User_Application_InstallLog.log holds results of the basic installation tasks.
-
Novell-Custom-Install.log holds information about the User Application configuration done during installation.