1.0 Identity Manager and Business Process Automation
The information in this section identifies some of the business processes you can automate through the implementation of a Novell Identity Manager system. If you are already aware of the business automation solutions provided by Identity Manager, you might want to skip to the technical introduction provided in Section 4.0, Identity Manager Architecture.
Managing identity needs is a core function of most businesses. For example, imagine that it’s early Monday morning. You scroll down the list of requests in your queue:
-
Jim Taylor’s cell phone number has changed. You need to update it in the HR database and four other independent systems.
-
Karen Hansen, just returning from an extended leave of absence, has forgotten her e-mail password. You need to help her retrieve or reset it.
-
Jose Altimira just hired a new employee. You need to give the employee network access and an e-mail account.
-
Ida McNamee wants access to the Oracle financial database, which requires you to get approval from three different managers.
-
John Harris just moved from the Accounts Payable department to the Legal department. You need to give him access to the same resources as the other members of the Legal team and remove his access to Accounts Payable resources.
-
Karl Jones, your own boss, saw a copy of Ida McNamee’s request for access to the Oracle financial database and is concerned about the number of people with access. You need to generate a report for him that shows everyone who has access to the database.
You take a deep breath and start in on the first request, knowing that you’ll be hard-pressed to keep up with all of the requests, let alone have time to finish the other projects assigned to you.
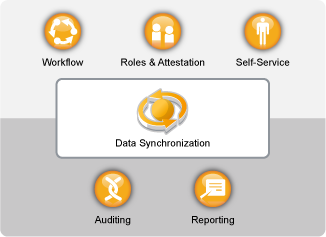
If this sounds like a common workday for you or someone in your organization, Identity Manager can help. In fact, the core Identity Manager capabilities, introduced in the following illustration, can help you automate all of these tasks and more. These capabilities—workflows, roles, attestation, self-service, auditing, and reporting—use multi-system data synchronization driven by your business policies to automate the processes involved in provisioning users and managing passwords, two of the most difficult and time-consuming duties of an IT organization.
Figure 1-1 Identity Manager Core Capabilities
The following sections introduce you to these Identity Manager capabilities and how they can help you successfully meet the identity needs of your organization: